The occasion was a 1950’s drunken Hollywood party. The leading men of the day were holding an impromptu contest of a certain form. Jackie Gleason famously shouted to Milton Berle: “Hey Miltie, do us all a favor and only pull out enough to win!”
In this chapter I will follow that principle. On the dictum that “a picture is worth 1,000 words,” I will start with somethingto end debate on whether Dominion machines are made in China:
Let us now turn to an analysis of the packet traffic on Election Day 2020 provided me by the best cyber-forensics specialist (aka “dolphin-speaker”) I have ever met. As packets travel through the Internet they leave a trail, and dolphin-speakers using the right tools can, in a sense, “shine a light” and reveal those packet trails in the cyber-fog. The cyber-specialists to whom I refer, who has access to such tools (and even more arcane ones), has documented vote-flipping in the Problematic 6 states amounting to 299,567 votes, just enough in each state to flip the election. 43% of that activity came from China.
For people who wish to study the data behind this claim, click here: US Election Fraud 2020_General For those who shudder at the thought of opening an Excel spreadsheet, this 1 minute video shows hundreds of foreign entities (many in China) who, on November 3, 2020, were conducting Man-in-the-Middle attacks on election system across these states of Pennsylvania, Michigan, Wisconsin, Arizona, Nevada, and Georgia in order to flip votes.
Now let us turn to a statement by a retired senior military officer that lays things out rather clearly (there is a fair bit of “dolphin-speak” below, but if you read it slowly, most will make more sense to you than you may expect).
———————————————————————————————————–
Declaration of XXXXXXXX
1. My name is XXXXXXXXXXXXXXXXXXXX, and I am a resident of XXXXXXXXXX. I hold an MBA from XXXXXX University, and a Bachelor of Science from XXXXXX University. I am retired from the US Army where I worked as an Air Cavalry Officer, a Psychological Operations Officer, and Information Operations Officer. I specifically conducted Special Technical Operations, analyzed and applied All-Source Intelligence to operational requirements. With a specialized team of military members, I helped author the Joint Urgency of Needs Statement for the CAUI EXORD (Countering Adversary Use of the Internet) and stood up the first two special category cyber-enabled operations under a unique Secretary of Defense authority. I am currently the manager of a Cybersecurity Company based in Texas. Our emphasis is on digital forensics and incident response (DFIR) cybersecurity, analysis of publicly available information (PAI), penetration testing of networks, and problem solving through operations integration. We use state-of-the-art tools and employ a wide variety of cyber and cyber-forensic analysts. My colleague and I are currently contracted to a cybersecurity and forensics firm that focuses on election systems.
2. We have examined the various Companies, Networks, Structures, Machines and related global infrastructures directly tied to the US Election.
3. This is a preliminary report on the various aspects of FOREIGN INTERFERENCE as defined by Executive Order 13848 issued on September 12, 2018.
a. Section 8 (f) defines the term “foreign interference,” with respect to an election, to include any covert, fraudulent, deceptive, or unlawful actions or attempted actions of a foreign government, or of any person acting as an agent of or on behalf of a foreign government, undertaken with the purpose or effect of influencing, undermining confidence in, or altering the result or reported result of, the election, or undermining public confidence in election processes or institutions.
i. There is clear and definitive evidence that foreign interference, as defined in the above Executive Order, occurred prior to, and during, the General Election on November 3, 2020.
b. In addition, Section 1 (b)(ii) states “if any foreign interference involved activities targeting the infrastructure of, or pertaining to, a political organization, campaign, or candidate, the extent to which such activities materially affected the security or integrity of that infrastructure, including by unauthorized access to, disclosure or threatened disclosure of, or alteration or falsification of, information or data.”
i. There is also clear and definitive evidence that foreign interference and unauthorized access to information and data, as defined in the Executive Order above, occurred prior to, and during, the General Election on November 3, 2020.
Dominion Voting Systems and Scytl/Clarity Elections:
4. Dominion Voting Systems is owned and controlled by foreign entities. We lose control of the data when it goes to a foreign country. For example:
• The electronic information went to Germany, Barcelona, Serbia, and Canada
• Dominion Servers in Belgrade Serbia. P 82.117.198.54 (ASN Range: 82.117.192.0/19)
• Dominion Servers ftp.dominionvoting.com with IP 69.172.237.100 (ASN Range: 69.172.236.0/22) is located in Toronto, Canada
• www.scytl.com with IP 52.57.209.147 (ASN Range: 52.57.0.0/16) is (was) located in Frankfurt Germany
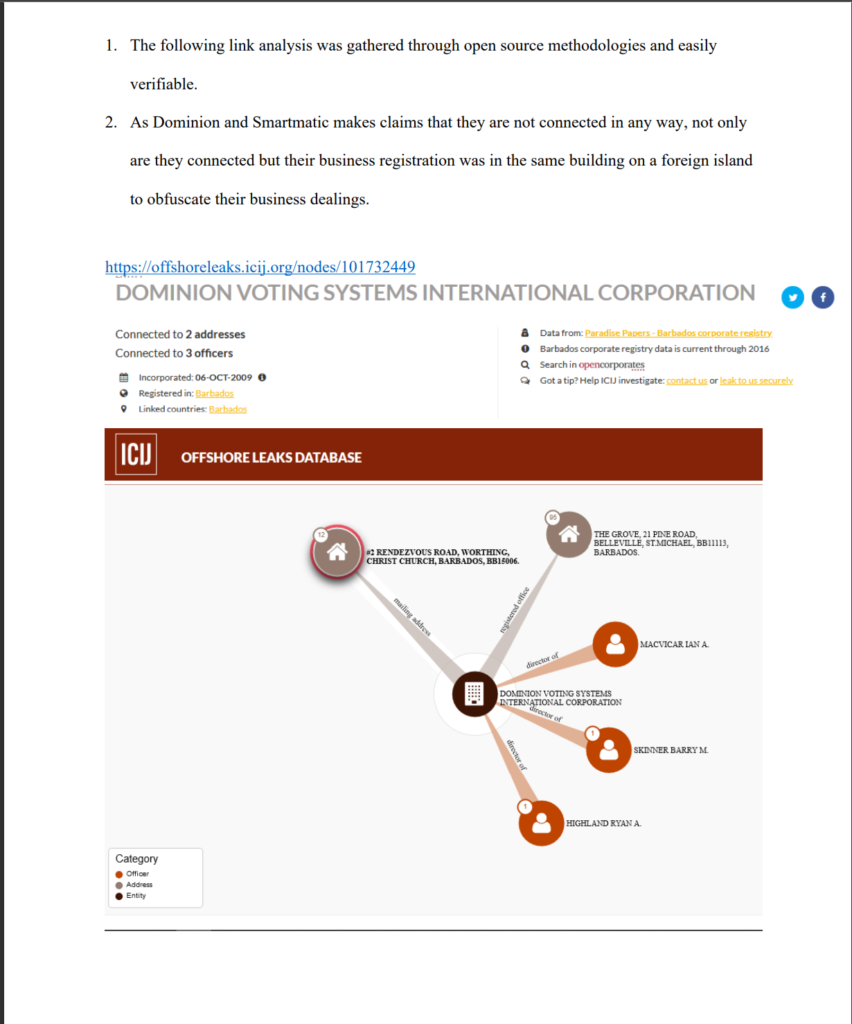
• support.scytl.com with IP 213.27.248.118 (ASN Range: 213.27.128.0/17) is located in Barcelona, Spain
• scytl-com.mail.protection.outlook.com with IP 104.47.10.36 (ASN Range: 104.40.0.0/13) is located in Ireland
• On election night the DE-CIX Frankfurt there was a 30% spike over the previous high rate of traffic. One stated probable cause was increased data flow to servers supporting the US Election.
Dominion Voting Systems and related companies are owned or heavily controlled and influenced by foreign agents, countries, and interests. The forensic report we prepared found that “the Dominion Voting System is intentionally and purposefully designed with inherent errors to create systemic fraud and influence election results”.
5. The system intentionally generates an enormously high number of ballot errors…The intentional errors lead to bulk adjudication of ballots with no oversight, no transparency, and no audit trail. This is the exact type of issue that leads to voter and/or election fraud.
6. The report found the election management system to be wrought with unacceptable vulnerabilities— including access to the internet— a key indicator to find evidence of fraud, and numerous malicious actions.
7. The numerous similarities will find that Dominion Voting Systems, Smartmatic, Electronic Systems & Software, and Hart Inter Civic, Clarity Election Night Reporting, Edison Research, Sequoia, Scytl, and similar or related entities, agents or assigns, have the same flaws and were subject to foreign interference in the 2020 election in the United States.
8. These systems bear the same crucial code “features” and defects that allowed the same outside and foreign interference in our election, in which there is the probability votes were in fact altered and manipulated contrary to the will of the voters.
a) Each of the companies use EML (Election Markup Language) and are susceptible to cross site scripting attacks (XSS) as described on page 7 in the Joint Cybersecurity Advisory.
i) Cross-site scripting (also known as XSS) is a web security vulnerability that allows an attacker to compromise the interactions that users have with a vulnerable application. It allows an attacker to circumvent the same origin policy, which is designed to segregate different websites from each other. Cross-site scripting vulnerabilities normally allow an attacker to masquerade as a victim user, to carry out any actions that the user is able to perform, and to access any of the user’s data. If the victim user has privileged access within the application, then the attacker might be able to gain full control over all of the application’s functionality and data.
b) Most, if not all, related sites were created using WordPress. WordPress currently has 2,675 CVE (Common Vulnerabilities and Exposures) listed on cve.mitre.org.
i) I performed a OpenVAS Vulnerability assessment for both Dominion and Scytl. There were multiple issues related to, out-of-date plugins and themes, which leaves sites vulnerable to attack.
c) With the various mergers, acquisitions, license agreements and partnerships the entire Election ecosystem in the United States is one and the same of any other Country where these systems are based, created, designed, used and so on. Namely Venezuela and their investment into Smartmatic.
d) Dominion’s purchase of Sequoia Voting Systems from Smartmatic has resulted in the same “Source Code” being used today.
e) During the Forensic audit we observed WinEDs and GEMS in the Dominion Voting System EMS (Election Management System). Both of those modules have been included in adverse findings from the EAC but are still in use today.
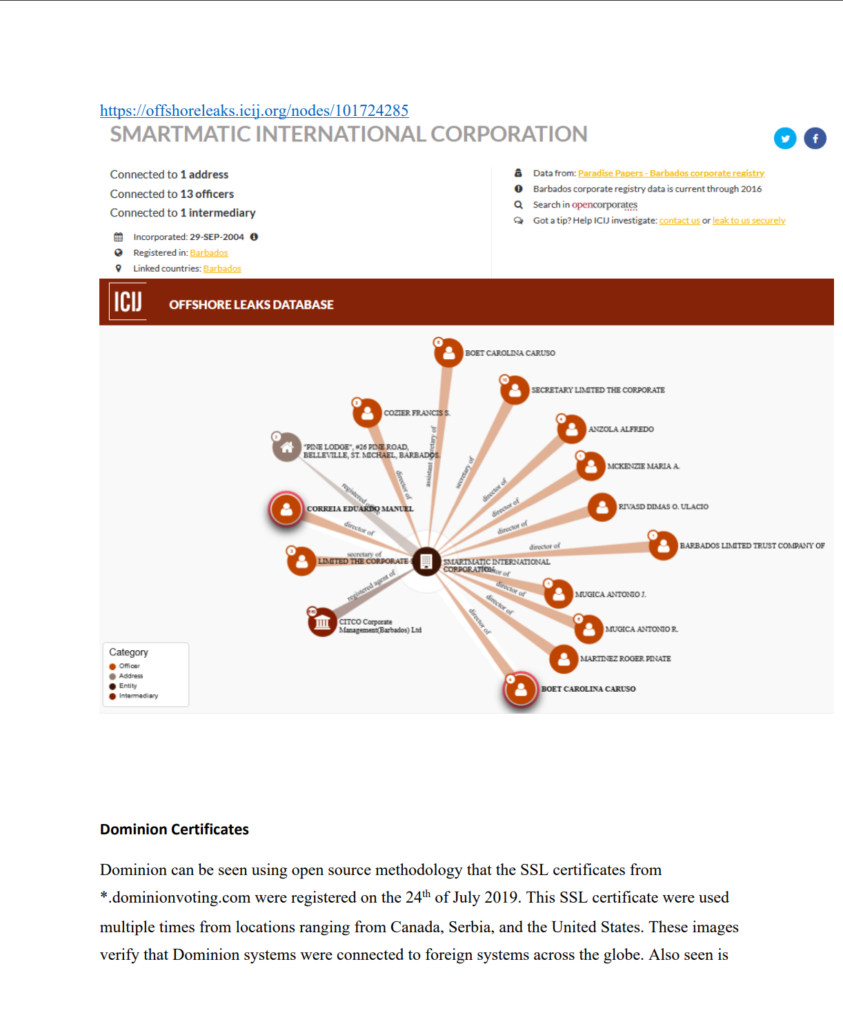
f) With the overlap between Dominion and Smartmatic, including the shared address in Barbados, the FCC Report ID: 2AGVK-VIU811 issued by the CCIS Lab in Shenzhen, China is very concerning. The Voter Identification Unit report was issued on July 23, 2020 and would give China insight on how to exploit the voting machines used in the US Election.
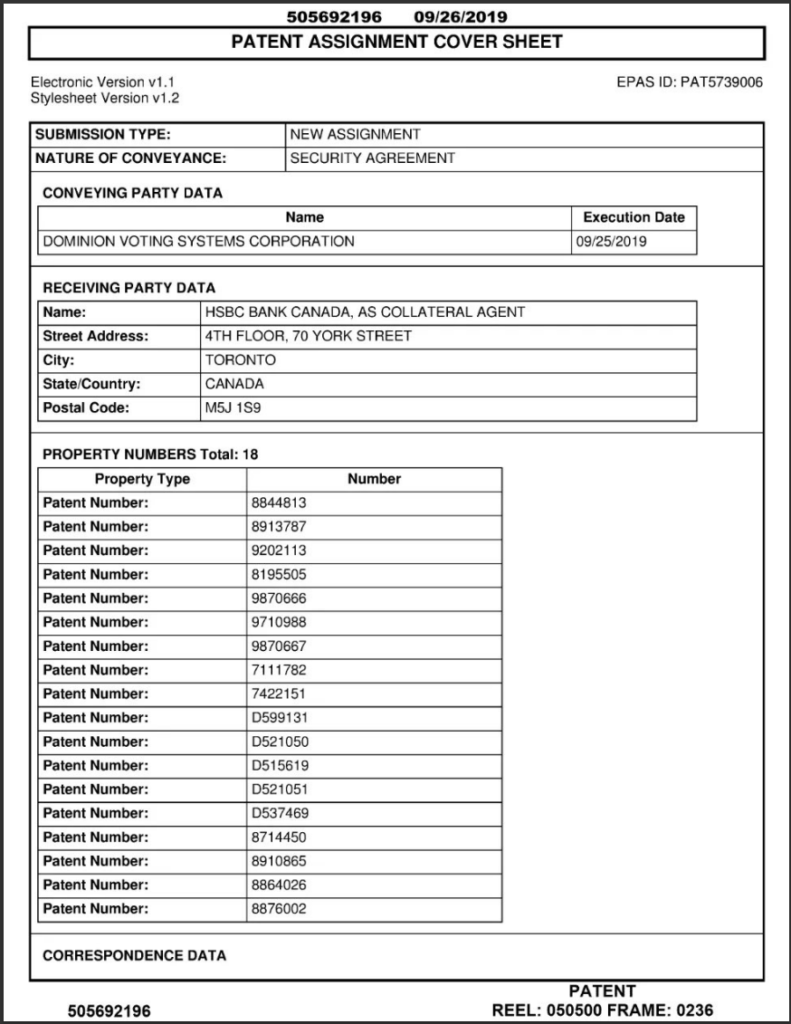
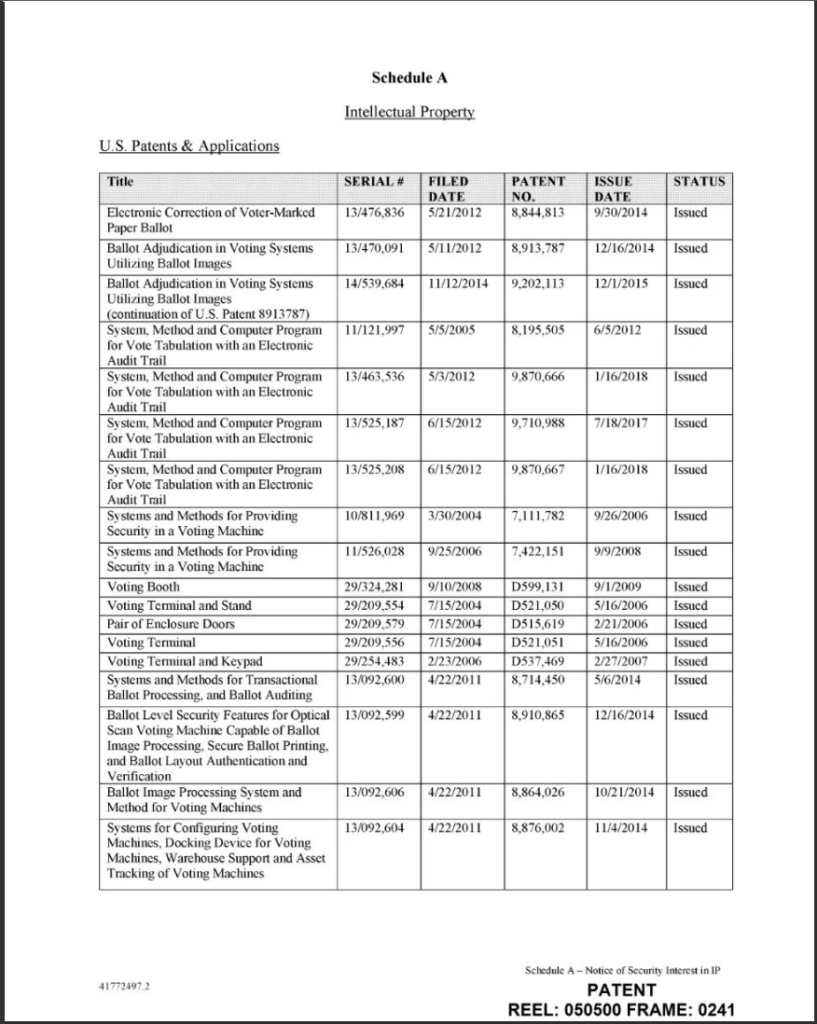
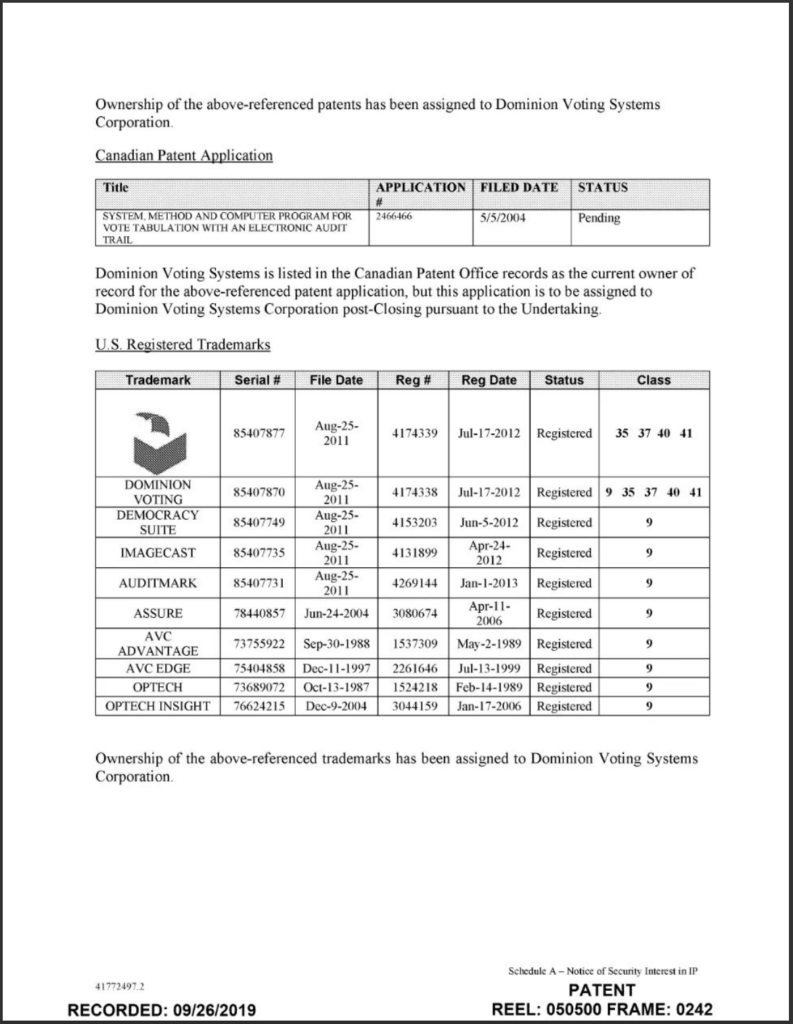
9. Dominion Voting Systems is based in Toronto, Canada, and assigns its intellectual property including patents on its firmware and software and trademarks to Hong Kong and Shanghai Bank Corporation (HSBC), a bank with its foundation in China and its current headquarters in London, United Kingdom.
10. Multiple expert witnesses and cyber experts identified acts of foreign interference in the election prior to November 3, 2020 and continued in the following weeks. In fact, there is evidence of a massive cyber-attack by foreign interests on our crucial national infrastructure surrounding our election—not the least of which was the hacking of the voter registration system by Iran. (E.O. 13800 of May 11, 2017)
11. This is compounded by the magnitude of the Solar Winds exploit that has exposed the private, public and government related companies and agencies. This includes the companies and agencies directly involved with securing our elections.
12. The FBI and CISA issued a joint Cybersecurity Advisory on October 30, 2020 (Report ID: AA20-304A).
a. This joint cybersecurity advisory was coauthored by the Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI). CISA and the FBI are aware of an Iranian advanced persistent threat (APT) actor targeting U.S. state websites—to include election websites. CISA and the FBI assess this actor is responsible for the mass dissemination of voter intimidation emails to U.S. citizens and the dissemination of U.S. election-related disinformation in mid-October 2020.1 (Reference FBI FLASH message ME-000138-TT, disseminated October 29, 2020). Further evaluation by CISA and the FBI has identified the targeting of U.S. state election websites was an intentional effort to influence and interfere with the 2020 U.S. presidential election.
13. Dominion and Smartmatic share a physical address in Barbados despite their insistence that there is no relationship between the companies. They also have a mutual non- compete agreement detailing shared resources and code.
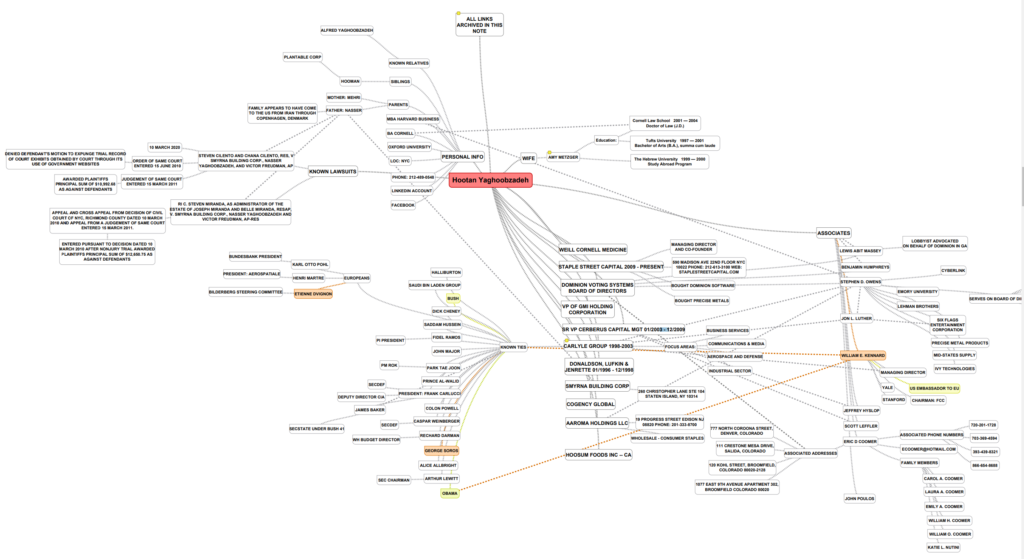
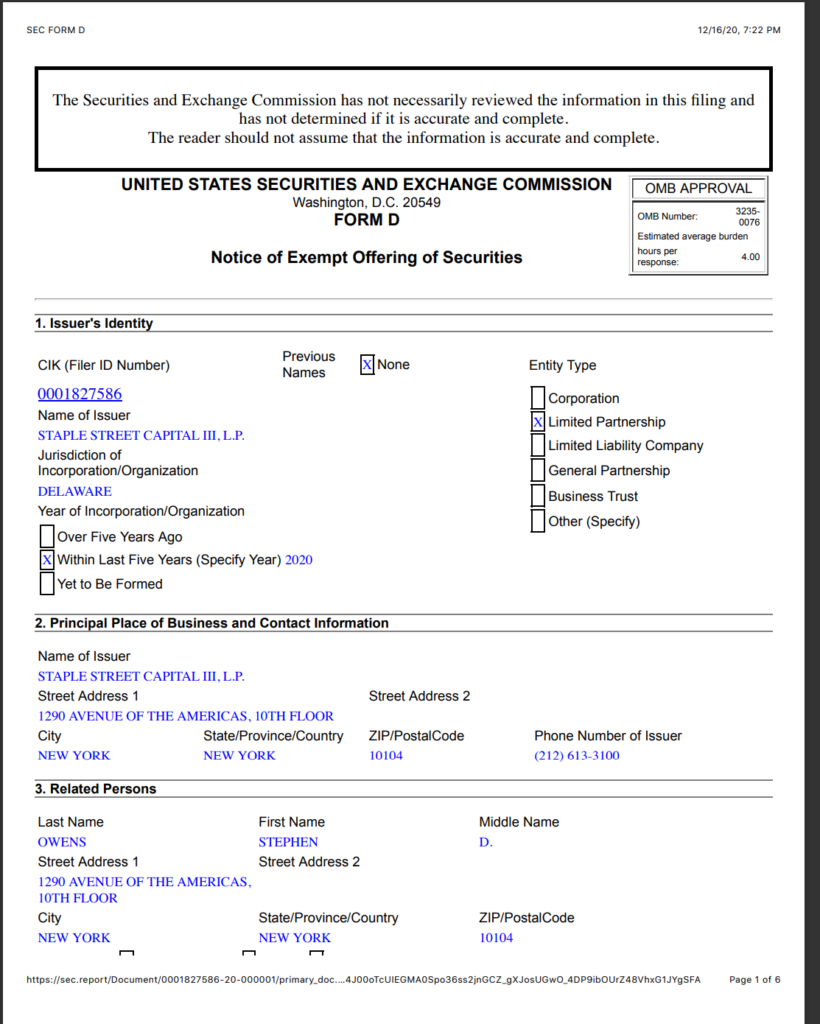
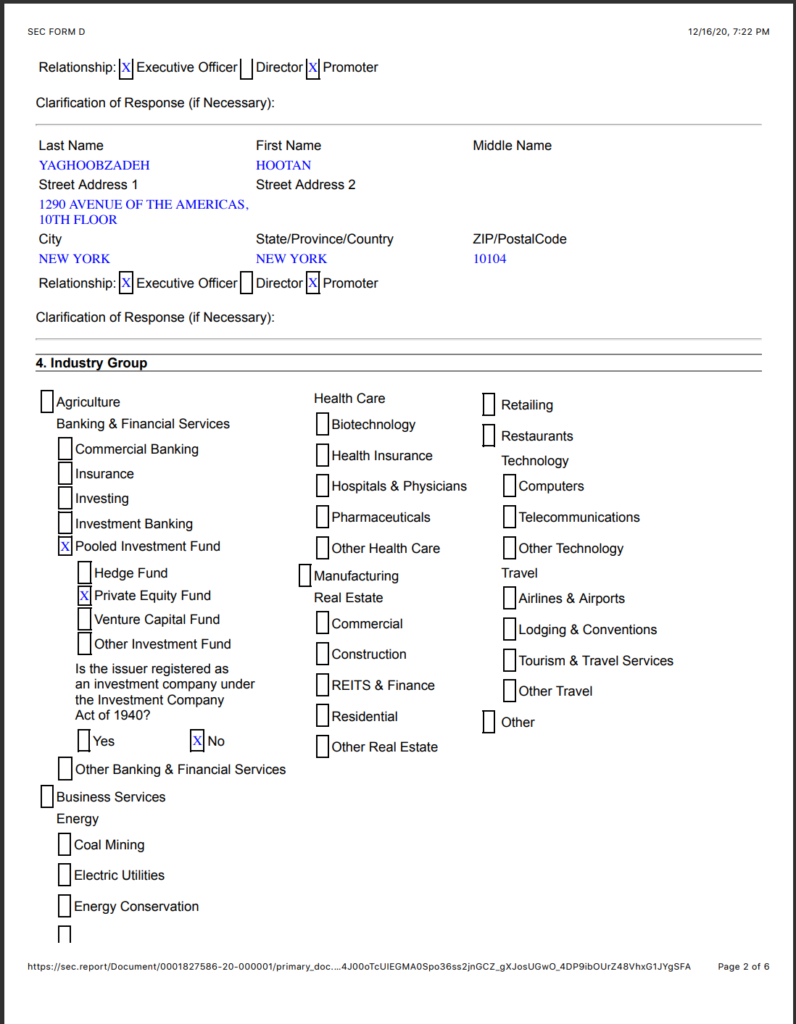
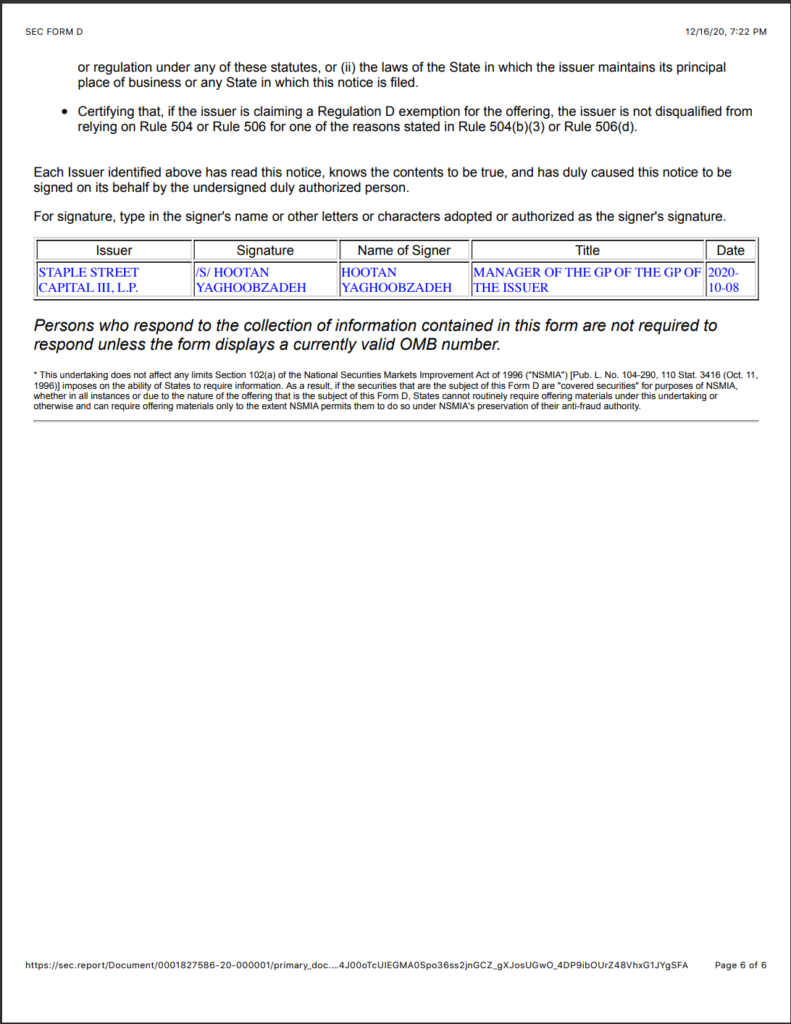
14. Hootan Yaghoobzadeh is the CEO and Chairman of Staple Street Capital, which is the entity that owns Dominion. Yaghoobzadeh was a close confidant to Sadaam Hussein and worked for the Saudi Bin Laden group. He previously worked at the Carlyle Group and Cerberus Capital Management.
Staple Street Partners
15. Staple Street Partners is a Private Equity firm that owns Dominion Voting Systems.
16. 9/25/19 – Dominion Voting Systems based in Toronto entered into a Security Agreement with HSBC Bank, assigning all intellectual property and assets including Trademarks, Patents and Software (see below).
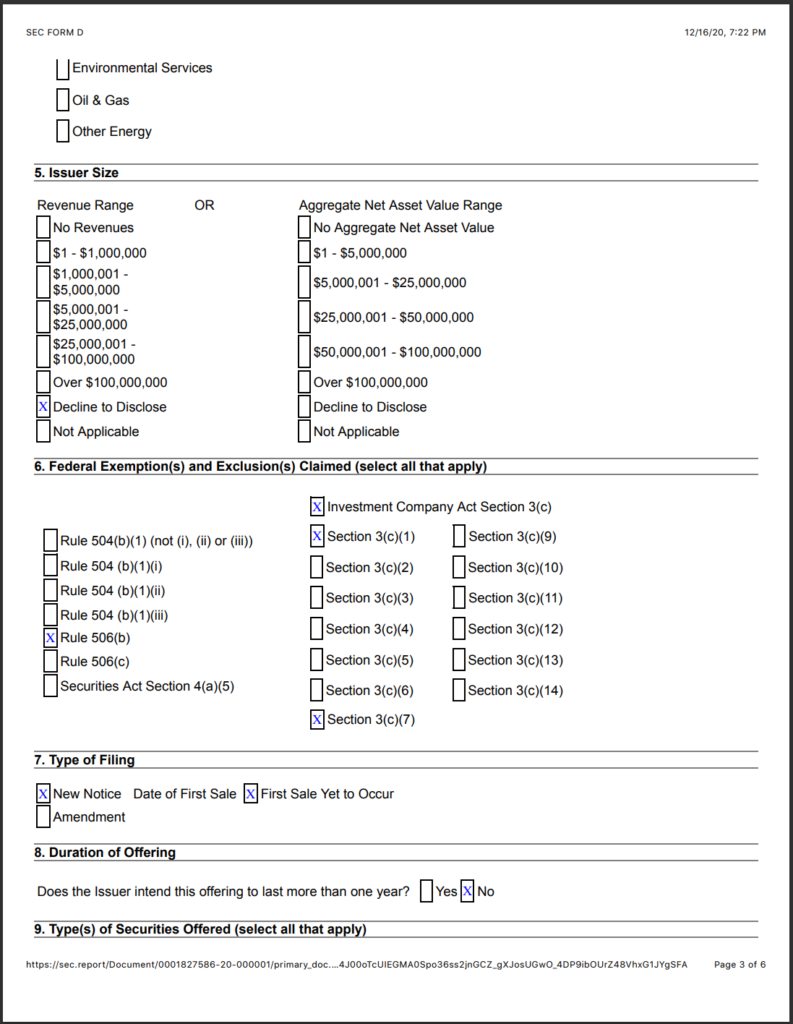
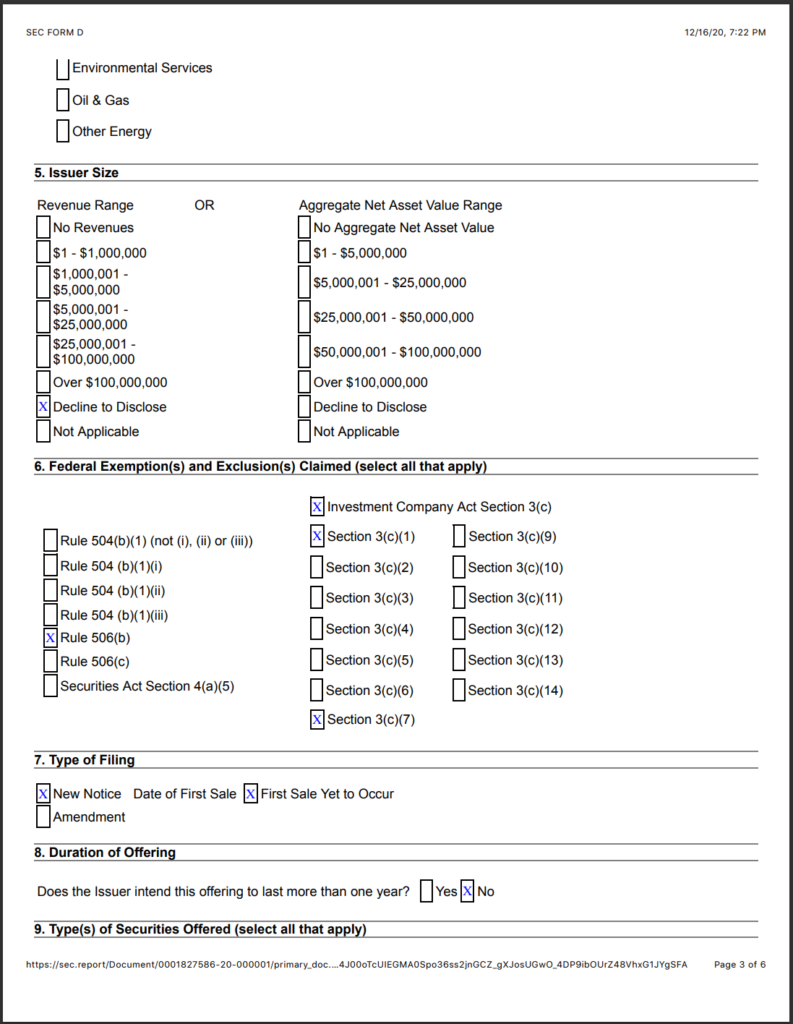
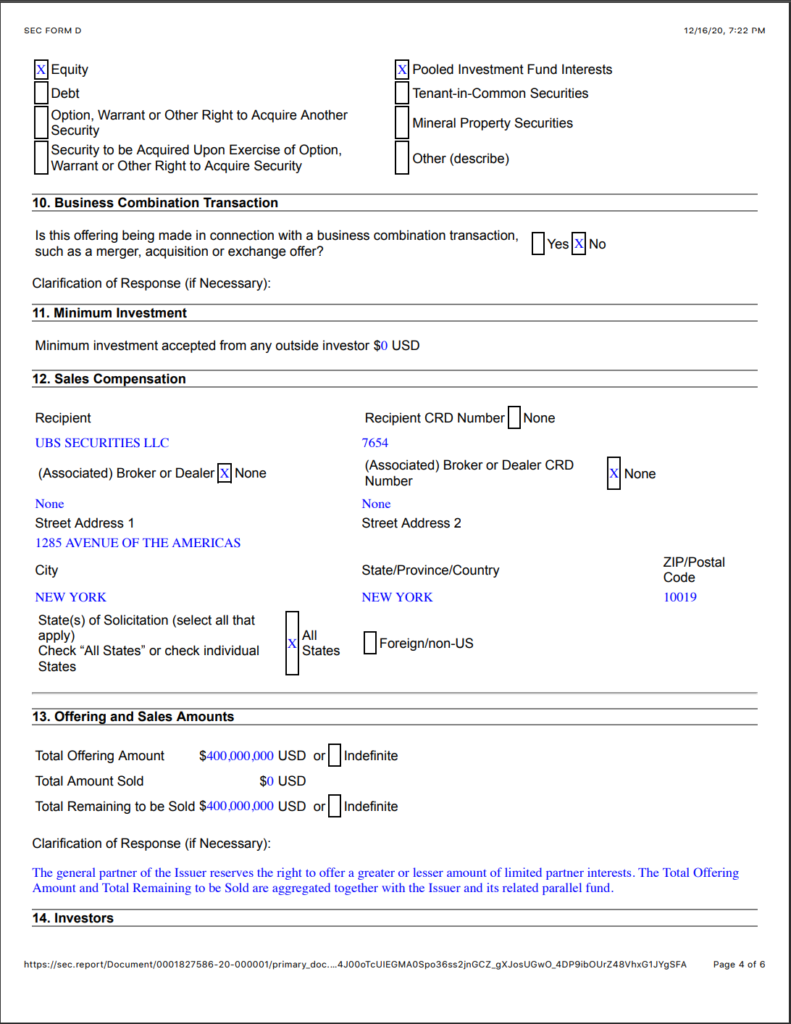
17. 10/8/20 – $400,000,000 from UBS Securities a Chinese managed subsidiary of UBS Global AG (see below).
18. Dominion shares an address with Smartmatic in Barbados (see below)
19. Dominion data is seen going to their headquarters in Serbia and Toronto.
20. The following link analysis was gathered through open source methodologies and is easily verifiable.
21. As Dominion and Smartmatic makes claims that they are not connected in any way, not only are they connected but their business registration was in the same building on a foreign island to obfuscate their business dealings.
https://offshoreleaks.icij.org/nodes/101732449
https://offshoreleaks.icij.org/nodes/101724285 Dominion Certificates
25. Dominion can be seen using open-source methodology that the SSL certificates from *.dominionvoting.com were registered on the 24th of July 2019. This SSL certificate were used multiple times from locations ranging from Canada, Serbia, and the United States. These images verify that Dominion systems were connected to foreign systems across the globe. Also seen is that the SSL certificate is used for the email server that was the same for the secure HTTP connections.
443.https.tls.certificate.parsed.fingerprint_sha256: 8f73a14d5f0fc10ebfa3086a99b9e7a550e822c71d762e627b73d12e5f1b8b9c
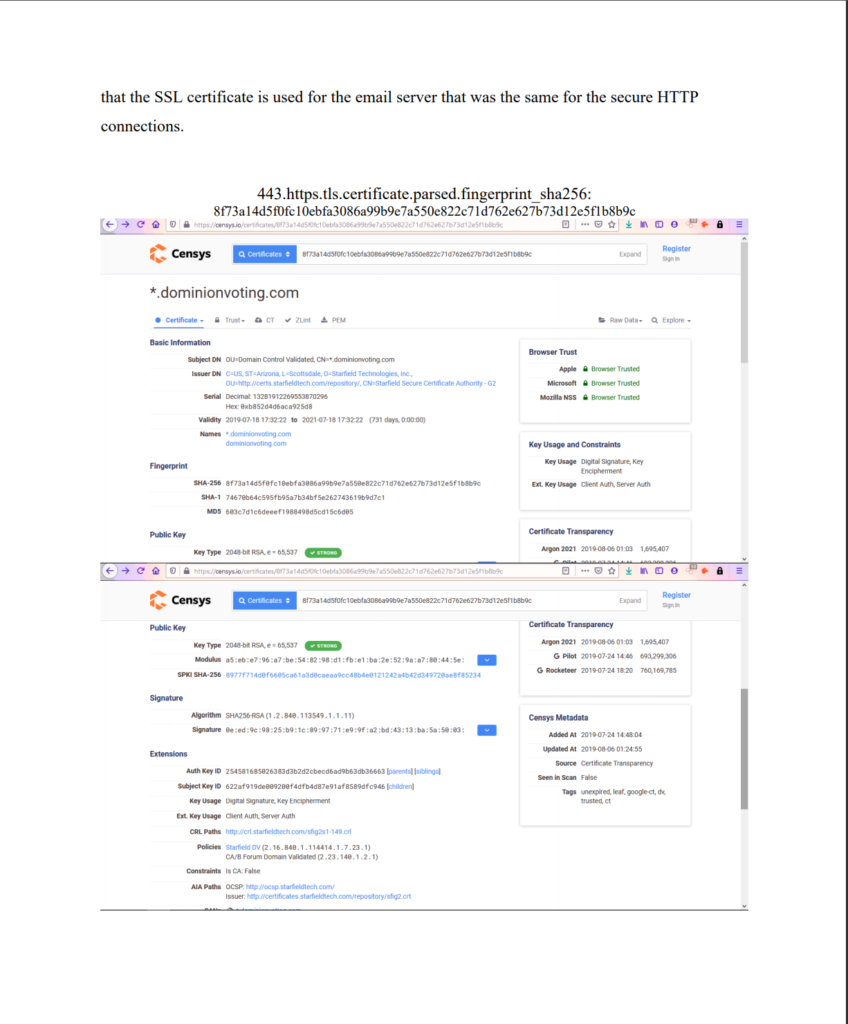
All share:
443.https.tls.certificate.parsed.fingerprint_sha256: 8f73a14d5f0fc10ebfa3086a99b9e7a550e822c71d762e627b73d12e5f1b8b9
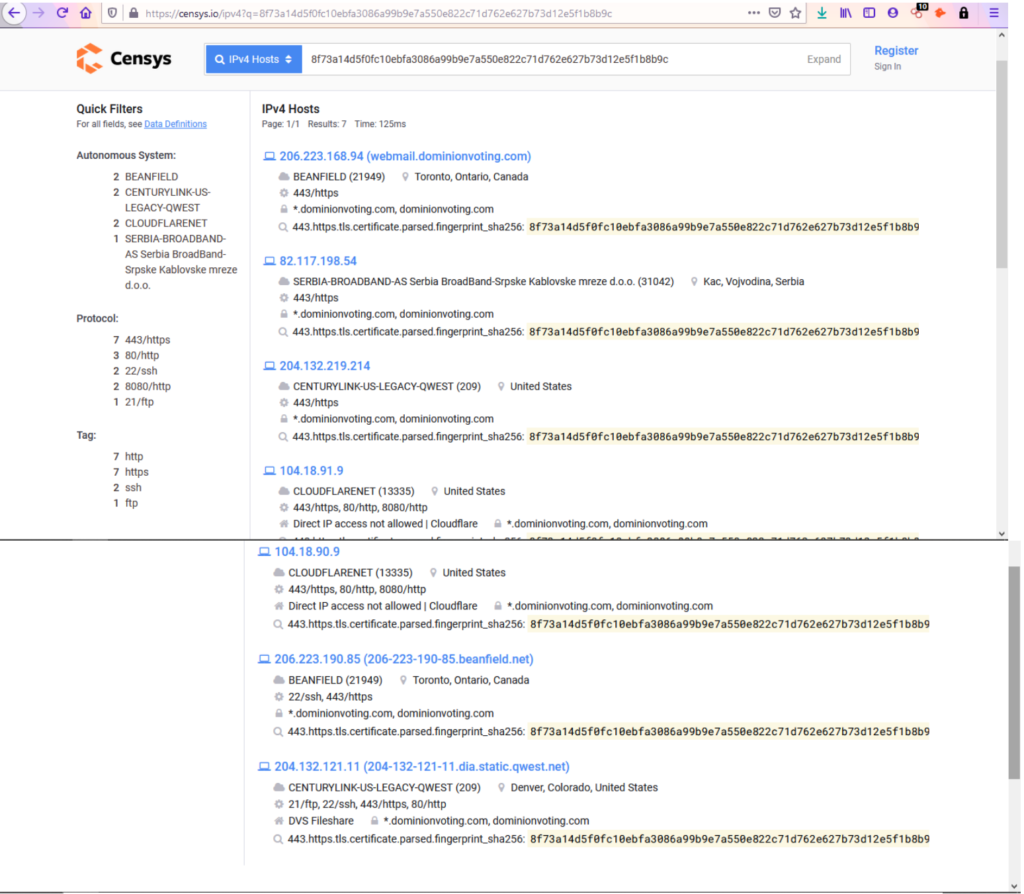
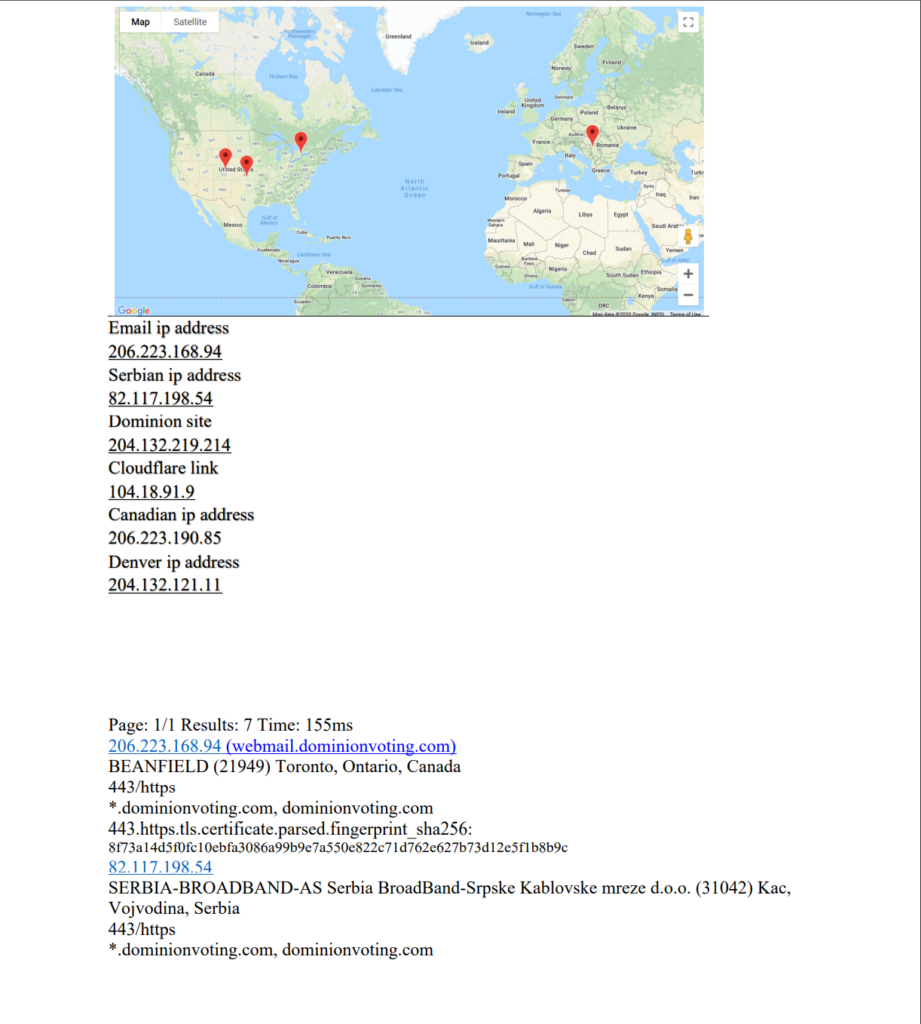
Email ip address: 206.223.168.94
Serbian ip address 82.117.198.54
Dominion site 204.132.219.214
Cloudflare link 104.18.91.9
Canadian ip address 206.223.190.85
Denver ip address 204.132.121.11
Page: 1/1 Results: 7 Time: 155ms
206.223.168.94 (webmail.dominionvoting.com)
BEANFIELD (21949) Toronto, Ontario, Canada
443/https
*.dominionvoting.com, dominionvoting.com
443.https.tls.certificate.parsed.fingerprint_sha256: 8f73a14d5f0fc10ebfa3086a99b9e7a550e822c71d762e627b73d12e5f1b8b9c 82.117.198.54
SERBIA-BROADBAND-AS Serbia BroadBand-Srpske Kablovske mreze d.o.o. (31042) Kac, Vojvodina, Serbia
443/https
*.dominionvoting.com, dominionvoting.com 443.https.tls.certificate.parsed.fingerprint_sha256: 8f73a14d5f0fc10ebfa3086a99b9e7a550e822c71d762e627b73d12e5f1b8b9c 204.132.219.214
CENTURYLINK-US-LEGACY-QWEST (209) United States
443/https
*.dominionvoting.com, dominionvoting.com 443.https.tls.certificate.parsed.fingerprint_sha256: 8f73a14d5f0fc10ebfa3086a99b9e7a550e822c71d762e627b73d12e5f1b8b9c 104.18.91.9
CLOUDFLARENET (13335) United States 443/https, 80/http, 8080/http Direct IP access not allowed | Cloudflare *.dominionvoting.com, dominionvoting.com 443.https.tls.certificate.parsed.fingerprint_sha256: 8f73a14d5f0fc10ebfa3086a99b9e7a550e822c71d762e627b73d12e5f1b8b9c 104.18.90.9
CLOUDFLARENET (13335) United States
443/https, 80/http, 8080/http Direct IP access not allowed | Cloudflare *.dominionvoting.com, dominionvoting.com 443.https.tls.certificate.parsed.fingerprint_sha256: 8f73a14d5f0fc10ebfa3086a99b9e7a550e822c71d762e627b73d12e5f1b8b9c 206.223.190.85 (206-223-190-85.beanfield.net)
BEANFIELD (21949) Toronto, Ontario, Canada
22/ssh, 443/https *.dominionvoting.com, dominionvoting.com 443.https.tls.certificate.parsed.fingerprint_sha256: 8f73a14d5f0fc10ebfa3086a99b9e7a550e822c71d762e627b73d12e5f1b8b9c 204.132.121.11 (204-132-121-11.dia.static.qwest.net)
CENTURYLINK-US-LEGACY-QWEST (209) Denver, Colorado, United States 21/ftp, 22/ssh, 443/https, 80/http DVS Fileshare *.dominionvoting.com, dominionvoting.com 443.https.tls.certificate.parsed.fingerprint_sha256: 8f73a14d5f0fc10ebfa3086a99b9e7a550e822c71d762e627b73d12e5f1b8b9c
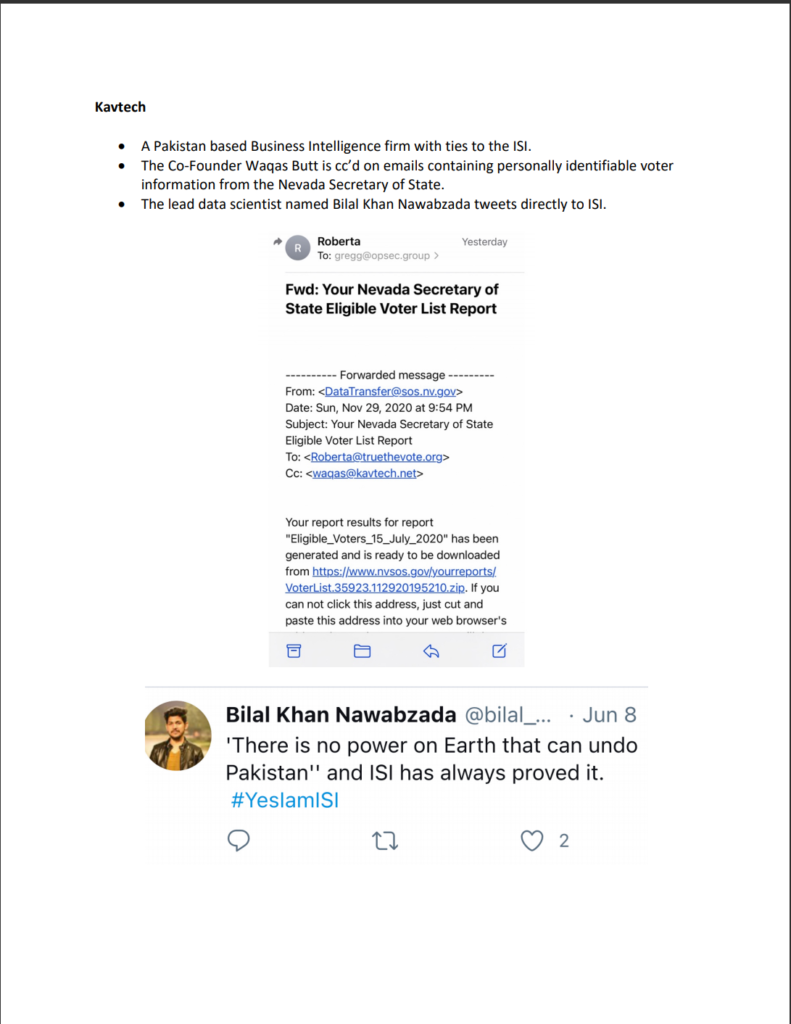
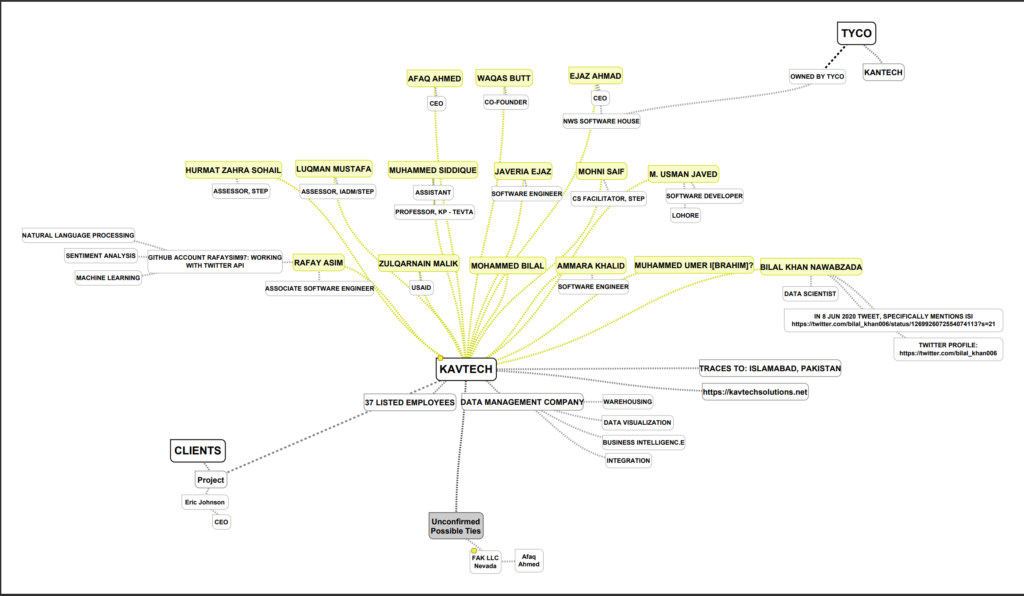
Kavtech
26. A Pakistan based Business Intelligence firm with ties to the ISI.
27. The lead data scientist named Bilal Khan Nawabzada tweets directly to ISI.
28. The Co-Founder Waqas Butt is cc’d on emails containing personally identifiable voter information from the Nevada Secretary of State.
a. This is a similar and deliberate act of unauthorized access of information and data as the hacking of the voter registration system by Iran. (E.O. 13800 of May 11, 2017)
29. Kavtech is a Pakistan based Business Intelligence firm with ties to the Pakistani intelligence ISI. The lead data scientist named Bilal Khan Nawabzada directly references Pakistani ISI in his social media.
30. Kavtech using Natural Language Processing and Sentiment Analysis to sway Voter opinion and intent to ultimately influence the election.
Supply Chain Concerns
31. One in five components used in voting machines are from China-based companies
32. On January 6, 2017 DHS Secretary Jeh Johnson on the Designation of Election Infrastructure as a Critical Infrastructure Subsector.
a. This means that election infrastructure becomes a priority within the National Infrastructure Protection Plan. It also enables this Department to prioritize our cybersecurity assistance to state and local election officials, but only for those who request it. Further, the designation makes clear both domestically and internationally that election infrastructure enjoys all the benefits and protections of critical infrastructure that the U.S. government has to offer. Finally, a designation makes it easier for the federal government to have full and frank discussions with key stakeholders regarding sensitive vulnerability information.
33. With that in mind, it is incredible that the Election equipment used in the November 3, 2020 election was manufactured in Russia, China and undisclosed Asian and European Countries (see below).
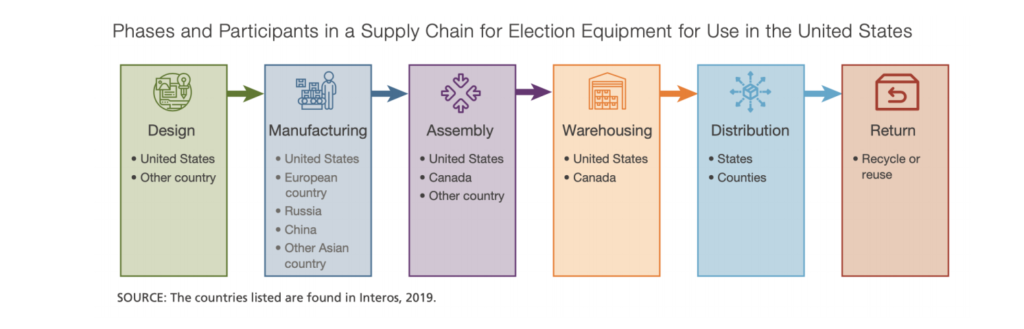
_________________________________
Reference:
https://us-cert.cisa.gov/sites/default/files/2020-10/AA20304A-Iranian_Advanced_Persistent_Threat_Actor_Identified_Obtaining_Voter_Registration_Data.pdf
https://www.whitehouse.gov/presidential-actions/executive-order-imposing-certain-sanctions-event-foreigninterference-united-states-election/
https://www.jstor.org/stable/resrep26524seq=13#metadata_info_tab_contents
https://www.dhs.gov/news/2017/01/06/statement-secretary-johnson-designation-election-infrastructure-critical
Now I could go much further. My dolphin speakers have had time to go much further than you have reviewed so far in this chapter (what you have seen thus far was generally prepared by or before Thanksgiving, November 26, 2020).
But I’m hopeful, Dear Reader, that I have above shown you enough to win.
Next Chapter is Chapter 3: Crashing the White House (December 18-22)









Patrick, Miles Guo the billionaire and anti-CCP whistleblower alleges you are a trained CCP agent spreading disinformation under the guise of that information being true to Trump and his lawyers like Sidney Powell. Do you have any comment on why Guo would attack you like this?
https://www.youtube.com/watch?v=gpe9VEwyYrk
and this may or may not be about you. But given your relationship with Sidney I thought he may also be talking about you.
https://www.youtube.com/watch?v=iEJ7yV37p6Q&ab_channel=%E9%83%AD%E6%96%87%E8%B4%B5
I think it’s more than likely that Byrne is intentionally presenting misleading low quality information from unreliable sources (ASOG is not a group of experts). Either that or he is partially insane. He even retracted his theory in the last part: “Do we know what really happenend? No.” and “There is not enough evidence to convict anyone”.
When I pointed this out on twitter, he immediately changed the lines. What a fraud he is. Trump knew it and his lawyers, too. That’s why Byrne keeps attacking them.
More generalization. Exactly what are your qualifications. You seem to know more then people who have spent decades working on this type of stuff.
How you ever worked on counter intrusion systems?
“misleading low quality information from unreliable sources” Do you have backup for this statement or better yet to you have high quality information that will dispute this “low” quality stuff?
you provide nothing, you contribute nothing. If you want to counter the information then do so with details.
So far you have been nothing but a blow hard….
Stop trollin
Patrick was banned from twitter on jan 15. Whomever you tweeting to IS spreading disinfo, but isnt him
To the Op who posted the youtube videos youre an idiot. The disinfo agent “famously publicly donated $250k to sidney” so thats NOT Patrick.
In the youtube Gao is talking about someone who famously and publicly donated $250k to powell. So NOT Patrick.
Sick to my Stomach that some POS in my Kanada did this to the Greatest Country the Earth has ever seen. Trump showed everyone HOW EASY it is to create a roaring economy. Politicians have lied to you for decades. When Americans have more Liberty, more Americans create independence from the State…can’t have that meow.
Democrats know this election was stolen but they always have to be right. They can’t admit their party has made suckers of them for decades. They should be pitied, not scorned. Maybe join the #WalkAway Dems and former Dems who will offer then support and succor in their distress and disorientation.
Well, except that #Walkaway is being censured and banned at every turn. As well as FBI arrested the founder…who knows. Whatever they could make up to get him.
Exactly. Nothing but another attempt to gaslight Mr. Byrne (or anyone else who dares to point out the truth). Those who have been paying close attention realize this.
Other efforts to analyze the 2020 election have yielded findings which are consistent with what Mr. Byrne has revealed thus far in his series of articles. Furthermore, the extreme efforts involved in blocking requests for independent audits of the physical voting machines would indicate that there is something which needs to be hidden by the perpetrators. In the few cases where legitimate audits have been permitted, the findings have shown to support Mr. Byrnes conclusions. In these cases, the enemies of the truth are left with no option but to attempt to discredit those who performed the audit; hence more gaslighting.
Worse things were done to those hundreds of brave souls who had the courage to sign sworn affidavits attesting to the illegal and fraudulent activities they witnessed during the election. If one examines the body of testimony delivered by these people to various state legislative groups/committees, they will find that it supports what Mr. Byrne is saying.
Mr. Byrne is not crazy. He is a courageous man and a patriot.
well said. legislative hearings in michigan and georgia did it for me
Byrne’s contribution is in a raw state, not terribly useful as is. The mediocre content however matches the quality of delivery so mediocrity, possibly caused by rushing, seems more plausible than intent to sabotage.
It is nevertheless odd that so many prominent voices speaking about the 2020 election fraud — which undoubtedly reversed the presidential winner — mix good and bad arguments to an extent that damages the case.
Byrne’s plan however, if feasible, made sense, which gives likelihood to him being on Trump’s side: use (possibly questionable) proof of foreign interference to force militarizing an independent audit of the paper trail.
That, btw, should be done even now, and it can be done like NYT and others were able to in 2000. It must include both ballots, and mailing envelopes, and must be started as soon as possible — there is s time limit of 22 months for retention.
The paper trail audit must answer the following questions about the presidential election, using manual (not machine) examination:
– do the envelope and ballot counts match what was recorded (and declared prior to audit);
– how many envelopes should have been rejected due to signature or improper registration;
– how many votes could have been altered by copying or by adjudicating a ballot due to (expected) automated read errors.
You’re all wack, you know.
Wow, I see the deep state is fighting back using tools like you and other operatives to try and deligitimse this information. Sit down an STFU. Try again moron.
Exactly. These swamp amoebas slime out of the sewers to discredit honest people trying to put out the facts.
In that youtube, Gao mentions agent who “publicly donated $250k to Powell”. So it’s NOT Patrick
The dominion machines have been used in other countries to steal elections. Witnesses have identical accounts of how they were used like in the US elections.
Yes they did. Michelle Malkin did a piece on how it was used in the Philippines.
ily
Secret agent or not, it’s a good read. What have we got to lose?What’s the truth or lie? We need clarification and hope. I choose to trust Mr. Byne. We gonna have to. Get thru this somehow!
So following him to here and discrediting his post will make him retract again?
Sowing doubt in the reader’s mind?
Traitors perspective is always contrary to verifiable facts.
Keep up the Fight Byrne
In those youtubes, Guo talks about agent who “publicly donated 250k to powell. So it’s NOT about Patrick!
Patrick is a real HERO! Patrick is American patriot! We love Patric! You Tyler are china guy working to destroy humanity pls. Go to hell with your communist boss.
Patrick you are a true patriot and hero for doing what you are doing. I watched every states hearings (AZ NV MI PA GA WI) on election fraud–hundreds of hours! So Im convinced the election was stolen. Anyone who claims the election was.not stolen or-Wheres the evidence–is an uninformed idiot.
One should question. Why is it that ALL GOOD PATRIOTS, like General Flynn, Sidney Powell, Mike Lindell, have had their Twitter accounts suspended/deleted by Jack Dorsey…so WHY does Patrick Byrne still have a Twitter account? Anyone who is on conservatives side or speaks out on voter fraud, has had their account suspended…why hasn’t Byrnes Twitter been deleted, or received any flags? Things that make you go hmmm
Maybe Twits or bots heard that Patrick is a libertarian so they left it up. I didn’t know Patrick still had Twitter. Good. It means I won’t have to join Telegram. Maybe he should put a link to his Telegram account before Twitter takes him down.
Former Secretary of State Mike Pompeo is still on Twitter.
Do you believe he is a spy?
Pompeo is the very definition of a Patriot in my view.
Pompeo should get off Twitter though, too.
“Maybe Twits or bots heard that Patrick is a libertarian so they left it up.”
Yeah, I don’t think so. It sure didn’t help Ron Paul.
Patrick was banned from twitter 1/15/20
It seems to have been temporary. Have a look yourself. He links to DeepCapture and talks about having a Telegram account.
https://twitter.com/PatrickByrne
Amen
I don’t understand why Patrick would continue to use Twitter when obviously Jack Doresy is part of this evil cabal trying to take down America.
I guess it comes down to Patrick not wanting to lose his followers but since he goes to such lengths at exposing the election fraud why not go all the way and just stop aiding and abbeting the enemy?
Some have lost their lives trying to expose what they’re doing like Seth Rich and others we will probably never hear about. Julian Assange is still a virtual prisoner because he dared to expose the Deep State and will probably be killed if he was ever released.
Guo is right. Ever wonder who was the source of fake Q claims that Lin Wood was making?
Let’s see you prove what Lin has said is fake. One of Lin’s eye witnesses was tortured but is still speaking out on what he knows about SCJ Roberts, Epstein, crooked DEA agents who planted drugs on people and killed informers.
Believe what what you want but when a person tries hard to convince others then that is a red flag to me.
One should question. Why is it that ALL GOOD PATRIOTS, like General Flynn, Sidney Powell, Mike Lindell, have had their Twitter accounts suspended/deleted by Jack Dorsey…so WHY does Patrick Byrne still have a Twitter account? Anyone who is on conservatives side or speaks out on voter fraud, has had their account suspended…why hasn’t Byrnes Twitter been deleted, or received any flags? Things that make you go hmmm
I do question things but I don’t agree with you.
“All” good patriots have been banned from twitter huh? Quite a statement. Pompeo comes to mind. Many others. So, no; not all.
Ok Anonymous
NSA’s Q group likely. Not too hard there.
Guo talks about someone who donated $250k to powell. So thats NOT Patrick right!!
I have read both chapters, excellent work. My issue is with this Chapter. It’s all great preliminary information but not proof of who did what.
1. China making parts, well China makes a lot of parts, (cars, tools, phones, etc) not a reason to claim foreign interference.
2. What did each of the countries do to change the election? We need Proof of what each of these countries did. Passing information through the internet is just that, but what did Germany actually do, what did the other countries do?
3. Patents and ownership is not a crime.
The only crime I see, is that States purchased this equipment knowing its foreign connections and ability to connect to the internet through thermostats and other means.
Unless you can show, Germany did this and Iran did that, we have no argument. Who, which country actually changed the votes?
Is that really so though?
In such a context…of secure elections…wouldn’t just the fact that the machines were connected to the net be sufficient?
And wouldn’t the fact that data was sent abroad, and, presumably, though it isn’t stated here, some was sent back, enough to corrupt an election?
Otherwise, why did Coomer go out of his way to deny, falsely, that DVS connected to the net?
Lila, I think people forgot that voting machines should not be allowed to connect to the internet. Absolutely not, that is a treasonous violation.
I agreed with you!
I agree. Foreign governments should not have been involved. Full stop. CCP and Democrat operatives are spinning hard because this is so damaging.
My worry is that this evidence, if more people become aware of it despite dinosaur and social media censorship, might trigger a false flag as a distraction. The so called Capitol riot will look like a picnic by comparison in terms of lives lost.
I believe they plan to do that anyway. They don’t have full support for their new Domestic Terrorism Act, so they need to invent something to outrage the general public even more. The new Act will be supported by all the Globalist R’s so it will be bipartisan. All Trump supporters need to be very careful the next few months. Everyone (R, D, I, L parties) needs to understand what they plan to do. That Act will be used to terrorize the public into absolute fear and compliance. They will use Special Ops groups to round people up. Everyone needs to protest this bill daily in whatever way they can that won’t be cause for the Uniparty to have them arrested as terrorists.
If it happened to the Dems the election would have never been certified.
I think after the election, it may have been Sidney Powell who said someone came forward and stated he was personally involved in the machine fraud and switching a large number of votes. I believe he was located in Italy.
Non Profit Who Broke the Obama Italy Election Intel = http://nationsinaction.org/
I saw that too, the guy in Italy. He’s the guy that actually did it. He came forward after he started hearing about suspected election fraud in the US. He realized that indeed what he was told to do amounted to interference in the election. Then a top attorney supposedly produced an affidavit. A picture of it was then posted. However, the document clearly had no official attributes such as letterhead, notary seal etc. Days went by and nothing ever came of it. I finally came to the conclusion it was a big farse. The whole thing seems to have dried up in a week.
No, it’s not dried up at all.
The affidavit was likely scrubbed for public circulation.
We are talking about crimes involving the highest levels of government in multiple countries, top ten defense firms, NATO officials. These people can destroy witnesses, bomb court houses and scrub the net, with impunity, so a little circumspection is warranted. The guy who did it, D’Elia was arrested, on trumped up charges, early in December, so that Leonardo could keep the whole business under wraps. The white hats are putting out some amount of disinfo just to keep things low profile, until everything is going their way, is my guess. You surely don’t expect them to tip their hands in public, do you? Big time mafia trials going on in Italy..that’s a clue….organizational shake up at the Vatican..another clue…Renzi withdrawing support for the gvt, Conte resigning…more clues..
Do you remember a prosecutor called Falcone…assassinated back over 20 years ago?
On or about Dec 4 or 5, I saw an original interview of a lady that was bringing all the info back from Italy. She had all the evidence that has since been talked about and then some. She was struggling to get the details to Trump Team. Needed funds to get it back. It was an amazingly indepth interview. I only saw it once and haven’t been able to find it again. She talked about bribe money tbe guy who did the actual vote manipulation/team of low level people, Leonardo, etc. She had all the details. As I recall she indicated that Trump Team was aware of her efforts. Therefore I actually thought that that was the big reveal that we were being called to witness in DC on Dec 6th. I listened to Trump’s whole speaking and was so disappointed not to hear anything about it. All we were hoping for was for Pence to do the RIGHT thing and send the Senators back for a review.
Big disappointment. Then our efforts were sabotaged and we were tricked into participating in a hudge conspiracy to undermine us and divert attention from the steal. It put us on the defense instead of the offense. Huge mistake.
Marie Zac – ItalyGate
They interfered by involvement at ANY LEVEL – even if they only took a cyber peek at what was happening in our election. Changing votes is not part of the criteria for “interference”.
https://www.youtube.com/watch?v=wzZRsXZ5Cz4
one ROM chip can change everything – made in china makes it even more likely – all parts are not equal
I can understand your need for detail on what every nefarious player did but for 4 years I watched and listened to the Left scream, Russia Russia Russia and to this day I have yet to see any proof that $200,000 in Facebook ads changed anyone’s mind on who should win in 2016! Bottom line We The People had the audacity to elect not select or install the next leader of the free world who just might put America First! The bonus was Promises made and kept, not so successful on Draining the Swamp and needed much more time! Sorry but anyone who believes that Joe Biden got more votes than Obama or that Trump lost with 11 million more than 2016 doesn’t have a brain-cell working! What probably shocks me the most about this entire sham is the total lack of intellectual curiosity demonstrating from the Left about our US voting system! As they say…its not about who votes, but who counts them! The end justifies the means?
Both those clips contain not one verifiable fact and comments are disabled. We’re asked to believe the translation word of same unknown chinese guy telling us Patrick is a CCP operative & everything is disinformation. I think not.
Well the person discussed by Guo “publicly donated to powell”. So, not Patrick
Well who knows what is going on, but this Miles Guo attack would explain why Steve Bannon is such as jackass on the machine angle of election fraud, being as Miles pays for (as I understand it) Bannon’s WarRoom.
I think Miles is talking about Jared Kushner
Good point. Bannon can’t stand Kushner.
Disprove it.
🤦♂️ special kind of naive, you are.
Thanks Patrick yes there is clear evidence we have enough to win. But we didn’t soooo…. Yeah, there are two things that we know for sure. joe Biden is in the White House and nothing has happened to give any sliver of hope any of this information will help turn over the election. With no visible action everything that has been pointed out is a conspiracy theory.
Patrick, take a closer look at the Kavtech/NWS Software House/TYCO connection made on the chart. It appears that TYCO owns Kantech (not Kavtech). Kavtech is definitely Pakistani, but that chart connection is probably inaccurate.
I hope Patrick will address/answer your question. I agree Guo is talking about Byrne (in 1st video linked^) but the second one…IDK, as Byrne isn’t typically talking about ‘God’ every day.
Hell, I don’t know who to trust. I am wary of Guo Wengui, aks Miles Kwok (rap iteration, IIRC), Miles Guo. I wonder how Guo is still alive if CCP is prone to murdering/disappearing (I do believe they are and do) anyone they need/want gone. ?? Guo was adamant, post-election, that TRUMP would serve 4 more years, would be victorious. He’s a bit hard to follow, often shares video w/o translation and then when there IS translation, seems parts are missing.
Bannon, who knows whether he’s trust-worthy. Nobody’s trust-worthy, lolol. Damn, but it feels like that’s true! My world: Ben Shapiro GONE, Laura Ingraham GONE, Sen. John Thune (my home-state SD), GONE, Jordan B. Peterson GONE, Douglas Murray GONE (By ‘gone’ I mean I just don’t trust them anymore, they were revealed by their actions/inactions post election.
Bannon…I did follow War Room, but wondered ‘Why’s the bumper music this Asian dude on a yacht, cigars, beautiful clothing….why doesn’t Bannon ever mention who he is, why he’s the bumper music?’ I started feeling like audience, myself included, were being HANDLED by Bannon…One day Bannon’s ” WE GOT THIS! TRUMP WILL SERVE 4 MORE YEARS”…next day, “Biden’s in, QUIT WHINING, let’s regroup, but no cry-babies!” Uhhh, OK. (just picture a middle-aged lady, mom, that’s me, not the least clued in, nor the most, either…I have read a lot though, Dostoevsky, most of the classics). I still trust DENNIS PRAGER, mostly because money isn’t the most important thing to him (and I know that in my bones, been following him forever). He doesn’t have all the answers either, though.
GUO, IDK. I just don’t know who is trust-worthy.
That’s really well said, my experience very much the same. What a political nightmare its been.
I don’t know what Miles said about Patrick, but his accounting of what transpired during his meeting at the WH with Sidney and General Flynn when he considered President Trump the “smartest man in the room” to a weak, pathetic loser makes no sense. It appears to me that Patrick has been thoroughly raked over the coals by his leftist family and friends. Beginning to sound like those talking heads on CNN and NPR radio.
His remarks about Trump being a “racist” because he claimed here were rapists crossing the border, or something to that effect. Well, Patrick, sorry to disappoint, but it is true. In fact, there are thousands of MS13 gang members who terrorize Americans (in LA alone, there are 58K gang members and most are illegal immigrants who came across our southern border illegally. NPR describes MS 13 as a harmless club. Please, spare me! Further, the part when he talks about Warren Buffet being charitable and helping Americans, how about Warren’s benefit regarding the cancelling of the XL pipeline, which destroyed 11K jobs with the stroke of Biden’s pen? Now the oil will be transported on Warren Buffet trains. Not a coincidence. Further, Buffet was bailed out along with other fat cats in 2008 with American tax dollars, while most Americans were left holding the bag. We received no help!
Patrick, if you are intending to morph into a Trump hating dirt bag, you will lose your Trump supporters. We are interested in saving America, not dumping on President Trump. And preventing the wall being built may please your mother and her rich leftist and liberal friends, because the caravans of people will not be moving into her neighborhood, but they are a huge burden on most Americans. They create extremely dangerous environments and terrorize people, especially the Hispanic communities, which is the reason President Trump is supported by large numbers of Hispanics. Further, the illegal immigrants receive more benefits than Americans, and cost us BILLIONS of dollars, which we need. But we are not all rich like Patrick, his mother, and Warren Buffet. What a bunch of arrogant snobs!
I’m disgusted and disappointed with you, Patrick! Go back to your mean-spirited, anti-American, liberal friends. Patriotic Trump supporters do not need you!
Absolute garbage you are spreading. People from around USA & the World came together voluntarily to help make since of Election Night Nov. 3rd. It took endless hours and sleepless nights to piece together the biggest election fraud in the history of the USA & perhaps the world. We get enough of this garage from our National New Media, you are peddling in the wrong place.
Congrats, Patrick. Your book has finally made a dent in those scumbags. The lawsuit means your book was super high quality and persuasive. They’re not getting a dime out of you, Mike, NMax Oan or anyone else. What they’re gonna get is some nice hard prison time. Thanks again Patrick, nice job………..www.smartcash1.com
It’s a bloody shame and this must be an accident prone voting system but what does it show in terms of winning or losing an election? Circumstantial evidence.
How is any of that circumstantial? Or did you not even read it? like every line not just zone out and scroll to the pretty graphs because your too lazy or incompetent to do a google search?
Are you Blind? Where were you. Have you followed the legislature for the last few months…or twitter/facebook or a press conference, you didn’t even read the article. Every question has been answered.
Vote dump on election night had impossible Biden-convenient inaccuracies in math…which only took a moment to match to similar foul play orchestrated in identical way.. in a different election..in a different place, on the same machines…with the mother company Smartmatic.
Our eyes were opened in Michigan with Dominion (name change since purchasing Sequoia/Smartmatic) This led to further investigation and obsession with similar inconsistencies and the links to anti Trumpers in highest places. Dominion was caught and there only option was to release statement saying they were in no way part of Smartmatic. (Who was implicated in Venezuela) This article proves connection x100.
Exactly right! As far as physical evidence of what votes went where and when, its easily identified by the Edison Research feed. Edison receives the time stamped vote tally information from the Dominion server and routes it out to NYT for one. The NYT feed is used by the MSM to show real time voting results. Surprised this is not often mentioned.🤷♀️
Why is this not being reported or even mentioned?
https://nationsinaction.org/2021/01/press-release-voter-fraud/
That is a VERY good question. I just posted a link to their site in this thread, too. 🙂
I have seen that information before myself. If i remember correctly thier cover up was “it was not enough votes to change the outcome.” Sorry, but that is not good enough for me. That was to pacify the indivduals that already belive the election is not corrupt. A blanket to quiet us all while the try to sweep it under the rug. We all know knowledge is power. Don’t let anyone steel it from you. It is just anothe intersection in the path the guilty hope we will choose the easy one so everything stays quiet.
Just to get this out of the way, I do believe there was industrial scale software-assisted electoral fraud.
That said, please be wary of any analysis based on Edison data feeds if they are 3-digit percentages rather than raw vote counts. 3 digits of percentage may not be enough significant digits to recover the raw vote totals. The computed totals are truncated and can result in what appear to be vote swapping. These two links explain what happens.
https://securitydebrief.com/2020/11/14/seeming-discrepancies-in-voter-data-fuel-for-disinformation/
https://www.metabunk.org/threads/claims-of-irregularities-in-nyts-edison-election-data.11450/
Well said, Kath.
As I read more and more and the evidence is clear, I keep coming back to the same question: understanding this, why didn’t the President act on this?
I suppose we will never know the answer to that.
Thanks Patrick for all you do.
I am In the belief that he has. And I don’t think all those soldiers are their to keep people out. Time will tell.
That’s my question, why didn’t the President do something? Did he know? Was he informed? Could he do anything? Now what? Are our “fair and free” elections over? Are we now and forever under a Democrat control? Will the 2022 elections going to matter? So many questions and no answers. There’s no one in control that will protect our freedoms, our rights, our Constitution. I still can’t believe that we let the Democrats take control. They didn’t win, we can see that but we let them push us down and take our freedoms. Like bully’s in a school yard.
There isn’t an island beautiful enough to deserve you, Patrick. How will we ever repay what you and your team have done?
Amen
Keep it comin Mr Byrne..
one in a quadrillion chance! Enough said
Clearly this was CIA using the AWS servers. You are overcomplicating everything. Those traffic packets all went over AWS location networks, which all point to shell companies to hide their true locations (Equinix, Interxion, E-shelter). https://www.peeringdb.com/ix/31. Bezos hates Trump after he tried to kill their government contract. CIA partnered with AWS in 2016 and now hosts the voting data and the voting registrations. They have it all. Scytl announced partnering with AWS, NCSWIC, and CISA in 2019. We will never have another populist president as long as we remain in the digital clutches of AWS and the CIA. Game over.
Thank you patrick for standing up and tell the people the truth. I truly appreciate what you are doing. Happy to know at least one man is willing to stand up and tell the truth. Its a very brave thing your doing Im sure many are not happy with you at this time so please be careful out there. I do have a question do you know why Trump handed the country over when he had all this evidence he could have used the military up to the last minute. Do you know why he didnt use the military was it just bad advice? I would think Trump would not listen to those who said give up dont use yours and the countries only hope. Or is there more to come? Does Trump still have a plan to fight the fraud and take the country back? Or is Trump done with fighting the fraud and Just going to fight be winning the country back by backing Republicans thats are running for the next elections and compaigning his come back in 2024? How will he ever win when the elections are all rigged. The democrats of control of every road back to the whitehouse. Trump will never win just running campaigns counting on votes to win in a rigged elections. If thats his plan its a doomed we are doomed its a plan that will never work. If you know he has a good plan please let us know. Can you tell us if his plan will work and it does or doesnt have anytbhing to do with the fraudulent elections of 2020 whatever you can tell you would be helpful. I understand if you cant give us details but some little hints or just letting us know there is one would be great. I wont to know if Trump is still fighting the fraud and if there is a plan to get the whitehouse back asap? Im worried that people are just hoing to wait to try to win the next election cause thats not going to work I know it amd you know it. The democrat communist party will just steal every election from here on out if we even have another election. Its looking like what we have is a dictatorship if thats the case there wont be another election….
Patrick I hope to hear back from you sorry about my long comment and writing skills are not my best abilities I suck at it lol But I hope you get where Im coming from Thank You, your greatly appreciated
God Bless You, be safe out there
Kat,
Stay tuned and spread the word.
Patrick I’ve sent your response to some friends who ridicule me of course. I sent them the Myron Fagan 1967 audio about What he thought the democrats were up to then. Shockingly close to the tactics that were used the last 20 years and led to this ultimate steal of our freedom. This runs very deep and has powerful entities behind it. How can you or Trump have a chance at such odds? I can tell your passionate about our country and what has happened. I’m afraid if Trump doesn’t have a military operating already then it will be a sad day for the Republic and for which it stood.
We all are, Patrick!
Kat, start watching https://x22report.com/
He seems to have an interesting take on events. You might become less anxious.
But remember, nobody knows anything for sure except the main players. Patrick, Flynn and Sidney only had supporting (but important) roles.
President Trump said the other day, “We’re not finished yet.”
Enjoy the show!
Pam, that was his caddie talking. Please listen again and tell me if you’re certain I am wrong. That wasn’t Trump’s voice. Then, another voice (also not Trump’s) added “Exactly”. I pray they weren’t talking about GOLF, but they may have been. Love your comments here, by the way. You and I are simpatico.
I listened again. Here is the clip. It’s Trump’s voice. Everyone else seems to think it’s Trump’s voice, too. The other two voices are different. If he was referring to golf then the followup voice “Exactly!” would make no sense. Those other two voices sounded louder as they were closer to the camera, observing.
https://www.youtube.com/watch?v=XdOioJ5xHGM
Cameraman: “Mr. President, thank you for your service, sir.”
Trump: “Thank you very much. *slaps leg twice* We haven’t finished yet.”
Cameraman: “Good, good”
Some other guy: “Exactly”
This makes no sense in the context you speak of. I am certain you are wrong.
I’m with you Kat! You said it all!
Do NOT waste your time on X22Report.
It’s pure fantasy, and it’s a waste of time for Patriots.
I agree that is probably true for the short financial videos about the Central Bank. But it’s always good to consider other points of view presented on his other, political videos.
JB is right. X22 is completely off. If it ever give a correct prediction, it is either an obvious one, or pure luck.
Yep exactly Nothing but QAnon nonsense !!
Agree. All these foreign addresses mean nothing, this was Deep State all the way.
The real question is: was Trump in on it or not?
So far, we still have no clear idea one way or t’other.
What is the significance of the peeringdb.com page, please?
Wow
So I just don’t get it. There is TONS of evidence and yet Biden is in the WH rip pin’ thru EOs putting all of his crook-buddies in key positions and killing our country!?!? What the heck!?!?
If you read the previous chapter, you’d know that Trump was kept in the dark almost entirely. For four years, besides the election, he’s been listening to Jared Kushner way too much (and being a stooge for Israel due to this (though every president for decades now has been like this with regard to Israel, and I’m not anti-Israel, merely anti-one sided alliances and anti-dual citizens being allowed to be politicians)). Trump could have been better, but he’s old. His main confidants were all exploiting him for their own gain. The people who cared were never brought before him, so there was never a chance for him to know.
What does Israel have to do with this? America and Israel are allies because they share the same democratic principles and agenda. If you are suggesting that Israel was in on the election fraud, there is a bridge in Brooklyn I would like to sell you.
“Allies,” yep, in the same way that hyenas taking down a noble lion are the lion’s allies.
Israel’s version of democracy and America’s are a bit apart, I’d say, but any criticism of this special relationship provokes cries of anti-Semitism and demotion to pariah status and since this is someone else’s platform, not mine, I won’t venture into it. Sufficient to say that it is this ENORMOUS blind spot that befuddles any attempt to expose the cabal or understand its machinations, because without delving into politically incorrect discussions, one cannot understand what is happening completely.
Dual citizens? Like you and iran?
How come all the cyber security experts didn’t pick up the Italian interference, which supposedly they confesssed to & led to the collapse of their government?
The algorithm was sent through a military satellite purposely to disguise its origin.
There was some effort to conceal it.
Who said they didn’t? I just have not written about everything.
The Italian affidavit with the whistleblower who admitted he was the one who administered the vote-switching software (I think it was, I could be wrong on the exact method) was always a big deal, though. It was proof that vote switching had been done and Italy was involved. Why that evidence, which was presented to Congress on Jan 6th before they voted, was ignored is beyond me. So frustrating to not really know exactly what happened. But Italy’s part does seem important. Nations in Action were the ones who got that evidence.
I guess most people who know about the Italian affidavit see it as the most damning piece of evidence. A confession by someone claiming to have been involved in the steal feels like the one thing that cannot be disputed. Stick that man on television and let him make a deal by turning over the names of others involved. He claims he has evidence of the original data and how it was changed. It feels like the lynchpin that ends all doubt.
Are we wrong to feel that way? The putt feels shorter than 3 feet when you add Italy. It feels like we could just ask Italy to pick up the ball and drop it in the cup for us.
Secret agent or not, it’s a good read. What have we got to lose?What’s the truth or lie? We need clarification and hope. I choose to trust Mr. Byne. We gonna have to. Get thru this somehow!
Aren’t there ANY decent people on the Democrat side?
How can they see this stuff and not want an inquiry?
It’s way beyond any particular election. It’s national security. It’s beyond even that. It’s the fate of humanity.
In that regard, is there any way to get the names of EVERY person involved in the war gaming effort run by the Transition Integrity Project [Rosa Brooks and Lawrence Wilkerson] and the National Task Force on Election Crises last year? Supposedly, it was bipartisan, but I’m betting the Republicans involved were only RINO’s, the Lincoln Project and the evil spawn of Gertrude Himmelfarb…
They of all people should be interested, but they won’t be, because their entire project was only to war game a scenario where Trump wouldn’t concede that he lost. They couldn’t, even theoretically, come up with a scenario where he WON, because, they already knew he was going to have it stolen from him.
The way they gamed out every possible response and how they were going to cry sedition and start rioting and seceding, is a tip off that they never once thought he would really win…and why? Because they’d cheated before, they were fixing to cheat again..and the only thing they wanted was to make sure the steal was secure.
I do not want to breathe the same air as anyone who cannot see this.
Your last sentence, exactly!
Lila:
I had done a little digging regarding republican participants at the TIP when it was released. Below is what I could find and I also included two guesses that I would bet were included.
(Confirmed):
Bill Kristol
David Frum
Larry Wilkerson
Ed Luce
Trey Grayson
Michael Steele
Max Boot
(My guess):
Jonah Goldberg
Andy McCarthy
Aren’t those all merely RINOs? I thought John Podesta et al. led the effort….
Thank you.
These guys must have known what was about to go down.
Trump supporters in Congress and voters should shun them.
Experiencing you write, a future must read/best seller, is in itself a pretty fricken awesome!
Sue
Sue,
Thanks. I hope some parts of the narrative are page turning. Some parts, like this chapter, are going to turn off any normal publisher.
‘PatrickmByrne’ vs ‘Patrick Byrne’ … posting under 2 accounts? or is there an imposter amongst us?
I think that was probably Patrick both times, forgetting he uses his middle initial only on Telegram.
…or he hit the ‘m’ key instead of the space bar.
…or he inadvertently hit the ‘m’ key instead of the space bar!
100% – I anxiously await for more. Patrick Byrne was instrumental in me letting go of the “hopium” and facing the (crappy) reality … it’s disappointing and incredibly frustrating that this was allowed to fully play out. Facing reality has stabilized my emotions (After dealing with the grief and horror of our circumstances) and GREATLY benefitted my walk with God again. Which is ironic since I don’t believe (?) Mr. Byrne is a believer. God used Him anyway. Putting our trust in man and systems of man will always disappoint.
Totally agree with this.
Patrick, thank you for giving us all a dose of reality. Your media tour after the meeting (and inaccurate NYT write up of same) really woke me up and made me realize what a lot of false hope we were all buying into. Hope is good; false hope is fatal. Thank you for all you’ve dedicated to this mission to find the truth.
Thank you, Patrick and company. Thank you, Allied Security Operations. Many of us had seen this material and were mystified that no controlling legal authority would act. Finally, through emails we urged POTUS to take action using his authority to seize machines and do audits and if necessary new elections in some counties. I was shocked and saddened by the picture of incompetence you portray in Chapter One and that more effective means could not have been found to prevent what amounts to a CCP coup of the USGovernment. I believe that a majority of voters know that the elections were rigged and stolen. I believe more citizens than anyone realizes have lost confidence in the ability of the US government to defend itself, its people, its economic system, and the Constitutional system of laws that govern us. People I know have said they are scared to lose our freedoms. I replied that I wish I could reassure them that there is no reason to be scared.
So in this part, you basically posted a video where someone scrolls down a spreadsheet (no data sources) and pasted an affidavit of a member of Allied Security Operations Group, a group of fraudsters. How does that fit the overall ‘narrative’ of your story?
By the way: How much does China pay you for this? Can I join? I’m good at writing confusing and unstructured texts, too. And I need the money, badly.
Don’t flatter yourself
@TrackerJ – You’re obviously too IMBECILIC to see the obvious FRAUD. Go back to playing in your sandbox.
If you need money, join Antifa. I hear they pay well. I’m sure there will be more false flags and riots to deflect from this information. Dem playbook..
Yes, another troll and useless waste of ——
If you use the IP lookup feature on Whatismyip.com, the IP addresses listed are legitimate. I’ve tested four (obviously I won’t bother with the entire list but you get me lol) I agree that I would like to see where he got it from directly, but on my judgement and ability to verify the IP themselves, I’m inclined to believe the list is authentic.
Miles Guo, eh?
Two can play that game.
https://www.miamiherald.com/news/politics-government/article232973237.html#:~:text=%E2%80%9CInstead%2C%20Guo%20Wengui%20was%2C%20and%20is%2C%20a%20dissident-hunter%2C,according%20to%20federal%20court%20papers%20filed%20on%20Friday.
Something tells me that it’s a safer bet that Guo’s the Chinese agent…
not Patrick. That whole video was so poorly done, the CCP should stop paying the guy. They’re not getting their money’s worth. But it makes me wonder about Bannon, who hangs out with the guy. I always distrusted Bannon..Goldman Sachs, intelligence background.
Let’s play a game, though. What if Byrne WERE a Chinese agent?
How does that change the IP addresses and data posted here? Why would a Chinese agent put evidence inimical to the CCP into Trump’s hands?
I’m not ready to write off Bannon. He gets in trouble due to his massive ego and alpha male, silverback gorilla (best hair in DC) personality. I don’t think he’s a traitor. His own daughter Maureen is in the military and often appears on his show.
OK…I like alpha male gorilla personalities and rarely have a problem with them.
It’s his Goldman Sachs background that bothers me.
Amazing analysis! If the voting machine fraud is not dealt with NOW, we will never have another election by and for the people again. What can be done, Patrick?
Think what can happen if everyone registered as a Democrat. It’s one small way, and the easiest way to move this mountain.
We’re all Democrats now!
Genius!
they are still can adjudicate your vote. This time is even much easier, they do not have to back feed the machines or connect to the internet!
But the votes would still be vulnerable to tampering/switching the exact same way?
Yes Trump was instrumental in greatly exposing the swamp and did a lot to thwart it and help We the People regain our country America First. But it wasn’t enough and we seem stuck with a Suspect Election and Apparent Bad Actors. There are more than just hints that Trump and his besties did not or could not overcome this, with at best poor talent and will and at worst some compromised acquiescence. Yet millions revere him and no other capable hero seems able and ready to take over fight. Leaving God will provide and such out of the equation, what is America to do Patrick? BASH OR CONDEMN Trump n Team? Revolt? Cry? Give up? WHAT???
The answer?
Keep moving forward and be smarter than the opposition!
I’ve always been very skeptical that so many were pinning all the hopes and dreams of our country on one man. Now we know he was basically alone.
Clearly and obviously Patrick, THIS IS ABOVE AND BEYOND evidence that this election was 100% stolen and the person that was sworn in at 11:48 A.M. on January 20, 2021 IS NOT THE PRESIDENT, Donald J. Trump is.
What can be done?
Thank you so much for all the ardent work and effort you and your amazing team have put into this. This is 1000% the most Patriotic assignment you have all taken on. The United States of America will not be stolen by foreign AND worst of all domestic TRAITORS!
Patrick is a real HERO! Patrick is American patriot! We love Patrick!
I’m guessing TrackerJ is a Chinese bot… spreading misinformation….Thank you for all your hard work Patrick and team.
This stuff was out on the internet more than a month ago…not in all the details, but enough to trigger action.
https://www.sgtreport.com/2020/12/foreign-election-interference-2-dominion-sent-information-election-night-to-5-countries-frankfurt-saw-30-spike-election-night/
Lila how can I find you on Telegram?
I know I opened a Telegram account sometime, but need to follow up on it.
I will probably lrajiva or lilarajiva.
Tracker j traces back to a foreign bot. They are scared.
Chinese sarcasm bot here. Beep Beep. Yes, we are very scared that Patrick is uploading more of undeniable proof (although he already retracted that he knows what’s going on or that he has proof). We are very concerned that he managed to uncover that we used an Italian satellite to switch votes, still somehow needed to work with Scytl and their server in Frankfurt (luckily, we won the gun battle, since they actually brought knives to the gun fight), still needed to work together with a plethora of other goverments (Iran, Pakistan, I forgot the rest, it’s so many, practically everybody was involved, so every country only needed to switch 666 votes, that’s how we operate) and on top of that we still introduced fraudulent ballots into the system.
Later on, we realized that was maybe a bit over-the-top and we completely forgot that one can easily proof our fraud by just showing spreadsheets with numbers without providing the data source. But hey, we are only humans, too.
Greetings from our command base directly under the Vatican.
Are you the TrackerJ in Bucharest, Romania?
https://www.instructables.com/member/TrackerJ/
Sounded like him!
You don’t need to know who committed a crime- or even how it was done- to prove there was a crime.
They knew Kennedy was shot because he had the bullet wounds.
Those spreadsheets and other graphs are evidence of abnormalities that are statistically impossible without human interference. They actually prove a crime was committed.
Even if we didn’t know who to prosecute, it is still enough information to demand the election be forensically audited or to be re-run without interference.
As long as there was a fraud, sooner or later it will be exposed! It has become a study project for all computers scientist! It will be exposed!
Thank You are a great Patriot !God Bless be Safe 🙏🙏
I’m a physicist who put together a team of statistical PhD Experts, to analyze some 2020 Presidential election data. We have now generated multiple reports like: , , , and . These support the implications in this article.
Feel free to send them to me.
I once briefly worked @ 1280 Ave. Of The Americas in NYC.
If that is what I believe it is: those are not actual offices of that business.
It is a front company hosting dozens of mailboxes, a few of people in front of computers, a couple of fax machines, etc.. -A sort of precursor to WeWork kinda scene..
I worked with a trio of people answering phones with sets of scripts/instructions for each client on whether to forward/route calls or express that the intended recipient of the call(s) are out of the office or unavailable, etc. taking messages and forwarding those messages via emails or fax..
More than once some seriously irate person would somehow get past the security downstairs and barge angrily into the office intending to confront a person that was not and had never been there on one matter or another.
Patrick: I just did. If you didn’t get it, I must not have your correct email. You have my email (when I signed up here) so email me to let know what your correct email is.
This illuminates what was obvious for the last four years – that there is a huge element of amateurism in Trump’s handling of the most important issues. The ludicrous amount of mailings from the Trump campaign for money even after the election was also unprofessional and counter productive. This started almost day one, when the FBI went after him and he reacted like Alice in Wonderland.
I am a EE ex-Intel and Bell Labs and had no difficulty following the narrative of the obvious steal. This narrative is utterly convincing when looked at in the context of the public pronouncements and the data supplied.
Thank you Mr. Bryne for your excellent and intelligent work and for writing this for the historical record. It was rather what I expected from an honest account.
My guess is Boris Epsteyn as the mediocrity, it fits his contact with Trump, profession and his childish narrative in the media.
Yeah there’s nothing here that wasn’t known or at least whispered about back in late November/ early December.
It didn’t require a PhD to immediately recognize so many layers of statistical improbabilities (essentially impossibilities) coupled with a completely rigged legal system.
The game is rigged. Has been for some time. At least now we see the extent of corruption in this country.
Still waiting on an intelligent answer to the question of ‘what do we do about it?’
And while I’m mildly entertained by these narratives produced by Byrne, I don’t expect he’ll have much of value to offer with regards to actual solutions.
Tim Pool said it best regarding Trump: the Left acted like he was Hitler, the Right like he was the Savior, when all we really got was a Kardashian.
I would like to alleviate Mr.Pool’s otherwise astute observation, with my personal one. Kardashian yes, but not quite, add a good helping of Emperor Constantine into the mix, if you know history.
Well, now your comment has broken me the rest of the way, let the healing begin. Kardashians HA
I spent a lot of time deducing who Mediocrity was, I thought it was pretty clear it had to be Pat Cx99@!!@&e. Patrick said in Ch1 it was someone with lots of Federal govt experience, etc. Epshteyn seems not to fit that particular criteria, though I cd imagine him projecting the right vibe…
I am at a total loss, and disbelief that all this and more is out there and again WHY Trump knew this is didn’t use everything in his power to correct this election!! It seems he gave up!….which is totally out of character!!! I don’t understand what happened and as the days go by and this unelected illegitimate person and his group of commies inflict damage on the American people, HE IS NOT THE PRESIDENT!! Cannot something be done???
Look, Trump is a smart guy. He and his lawyers knew very early that they are probably going to loose the litigation, although the elections in many states were conducted in an unconstitutional manner (see, for example, the Pennsylvania & the Wisconsin lawsuit).
They also knew that, although Dominion machines are a security risk, that votes hadn’t been switched on a massive scale, since it would have shown up in the recounts. That did not happen. And Byrne & loonies were never able to produce hard evidence of that, they just kept inventing new stories. Still, they pressed Trump to invoke some kind of martial law, it would have been the end.
So Trump & his team eventually distanced themselves from Byrne & loonies. There is still a bit of hope that the Supreme Court will at least acknowledge the unconstitutionality of the election next month, since those cases are still on. If lawful votes were counted, Trump would probably win Wisconsin and Pennsylvania. About Georgia, I’m not so sure. In Arizona there is going to be a forensic audit as Kelly Ward announced. So let’s see what happens.
Been reading your replies. You never mention General Flynn’s role in your response. Is he one of the “loonies” you refer to? I’m just a regular citizen but I just don’t believe that General Flynn would align himself with people who intend to hurt this country.
I don’t believe that Sydney Powell, General Flynn or Mike Lindell are intentionally hurting this country. A lot of normal people believed those theories and allegations. Someone was feeding Flynn and others disinformation. And they believed Martial Law would be the right answer to what they believed to be a coup.
Conspiracy theories can be convincing, especially if you have a non-transparent process like this election. I don’t say there is no fraud. I don’t say this was a fair election, because it wasn’t. I don’t say China isn’t happy about Bidens win or that they influenced this election in some form.
But the theories about massive digital vote switching are baseless. They exist because the New York Times data feed has some negative vote changes for the swing states. That’s like the only ‘evidence’ there is and people find that incredibly convincing. But you will find negative vote changes in states that did not even use dominion voting systems, like North Carolina. Or Texas, which Trump won. Or New York, where Democrats were expected to win by a large margin anyway. So why cheat there?
https://static01.nyt.com/elections-assets/2020/data/api/2020-11-03/race-page/north-carolina/president.json
https://static01.nyt.com/elections-assets/2020/data/api/2020-11-03/race-page/texas/president.json
https://static01.nyt.com/elections-assets/2020/data/api/2020-11-03/race-page/new-york/president.json
And on top of that no recount found hundreds of thousands of votes missing or switched. So at this point, I think the burden of proof lies with the proponents of the theory of massive digital vote switching.
In the meantime you should listen to Scott Adam’s podcast, he discusses these points pretty objectively.
I don’t believe that Flynn, Lindell, or even Powell intentionally hurt this country. They were fed disinfo that millions of other normal people believed, too. Without a functioning media that objectively examines the claims and evidence even the weirdest theories survive.
I believe there was some amount of fraud in this election, mainly caused by absence of safeguards in some of the swing states. Also, the removal of safeguards itself was unconstitutional. So is it enough to overturn the election? Probably.
But to this day I have seen literally nothing even remotely substantiating the idea of massive digital vote switching. People are basically in love with this idea because it’s so flexible. They don’t even notice the constant shift in Byrne’s narrative.
“Targeted” vote-switching is what has been demonstrated so far. See; Antrim County.
“Massive” vote-switching appears to have support via numerous sources:
1) . Scraping of Edison Data:
https://www.theburningplatform.com/2020/11/11/what-is-a-pede-dominion-voting-system-under-attack/
2) Dominion’s own MANUAL talks about how to BATCH VOTE SWITCH
3) The fractional voting system further shows the built-in capability to rig elections in Dominion/Smartmatic systems
4) the DEMOCRATS were screaming for years (decades if you include the Diebold allegations) that exactly this was likely to be going on — massive vote switching.
5) circumstantial evidence is quite damning — the to-the-death fight of elections supervisors to hide the machines, scrub the hard drives, delay in court, etc.
To JB and “scraping of Edison Data”. Pede was mistaken and later backtracked.
Be wary of any analysis based on Edison data feeds if they are 3-digit percentages rather than raw vote counts. 3 digits of percentage may not be enough significant digits to recover the raw vote totals. The computed totals are truncated and can result in what appear to be vote swapping. These two links explain what happens.
https://securitydebrief.com/2020/11/14/seeming-discrepancies-in-voter-data-fuel-for-disinformation/
https://www.metabunk.org/threads/claims-of-irregularities-in-nyts-edison-election-data.11450/
How’s the weather today in Beijing?
It’s lose, not loose. Common mistake of aliens.
If you can’t attack the message, attack the messenger. Common communist practice since Karl. Another one: Projection.
I call it Stalinsky tactics.
Just go to the yt inauguration clip and watch with no attendees and compare down with up votes.
But yeah, dementia Joe got the most votes in history. 80 mill.
If you believe that I can sell you a bridge with ocean view in Nevada …
I wish we had a George Washington. He would know what to do!
@G, half the people on the Internet misspell “lose” (confusing it with loose, like “Loose lips sink ships”, “Loose the dogs of war”). Also annoying is rampant misspelling of ‘border’ (in favor of boarder, “Mom was so broke she took on a well-paying boarder).
My grandmother, born in 1917, had no formal education past high school (she worked in the “sliced bacon department” of our local slaughterhouse) and was 5 times more literate than today’s typical ‘college’ grads. We should do better.
You obviously don’t understand how election systems can be hacked and how ballot tabulation occurs. The false count is built into the system and is going to produce the fraudulent ballots to support it using the ballot adjudication process. However, the original ballot images remain and could be counted.
Next, the vote switches are obvious in the election data reports (I know this because I did the analysis). Biden won Georgia and Pennsylvania because of vote switching. Michigan and Wisconsin were won through large injections of votes around 3AM. Pennsylvania and Georgia also experienced 3AM vote injections.
Prosecutors use coincidences like those to make their cases in court as “coincidences” don’t usually work out well for defendants.
Those who argue these “coincidences” came as a result of large urban areas being counted — in four states all at the same time — have not produced evidence to support their claims.
In fact, those claiming there was no fraud have done nothing but make legal filings to avoid having to argue the cases is courts. The judges have went along by using legal technicalities to avoid hearing the cases.
Clearly, we agree that the Arizona audit may be telling.
We also agree that SCOTUS should acknowledge that state Supreme Courts did not have the authority to change election laws.
‘The false count is built into the system and is going to produce the fraudulent ballots to support it using the ballot adjudication process.’
You do realize that adjudication is a digital process? You are not explaining why the hand recount did not uncover the (allegedly) missing hundreds of thousands of votes.
‘Next, the vote switches are obvious in the election data reports (I know this because I did the analysis).’
It’s literally not even in the actual data. You are looking at the Edison data source, that’s unprofessional. And ‘I know it because I checked’ is not good enough. Show us your analysis then 😉
‘Those who argue these “coincidences” came as a result of large urban areas being counted — in four states all at the same time — have not produced evidence to support their claims.’
What coincidences? There is literally nothing to explain. What you are referring to is the fact that there were large vote drops with a ~75-80% Biden share. If you look into the data, you see that these drops came from large urban areas like Atlanta, which have exactly those vote shares for decades now. What is there left to explain?
You are clearly someone who uses English as a second language. Your use of prepositions and tense is wrong, and resembles the English written by some Chinese friends of mine. Tell your handler in the Ministry of State Security that you need a grammar lesson.
I think Trump was hamstrung his entire administration by those around him. And they went into overdrive and their last gasp for the election. I don’t think any of us understand or can grasp how deep and corrupt the entire system is, and how it closed ranks to take Trump down. The miracle is it took five years.
This article from Conservative Treehouse explains a lot: “Robert Mueller had two goals as special counsel. Goal #1 was to continue the fraudulent DOJ/FBI “Stop Trump” operation initiated by James Comey, Andrew McCabe and their crew technically named Crossfire Hurricane. Goal #2 was to bury the illegal action; to create the cover-up needed for everything that took place in the “Stop Trump” operation.
It is the second goal that most people never reconciled; however, it is also that second goal that’s the most important. Everyone in DC knew Mueller’s objective. Every person in every branch of government and every federal agency knew Mueller’s real purpose.”
https://theconservativetreehouse.com/2021/01/30/systemic-contingencies-they-all-knew-lessons-from-spygate-about-severity-of-dc-corruption/
The Treehouse has done a great job on this!
But I still have one question: how the heck has Adm. Mike Rogers remained silent for 4+ years? The biggest shock to me of all.
Donna, I believed that there are many peoples like you out here. That why we keep on searching for pieces
of information hoping that will reveal the truth.
And here we are! hopefully, we might find it here at Deep Capture.
I agree that you don’t understand what happened so are upset. Where is your evidence that President Trump just threw up his hands? He said, “We aren’t finished yet.” He couldn’t just send in the military because the media and the permanent political class would have called him a dictator. We might have had China on our doorstep protecting their investments or the UN blue hats. This way the military will appear to act unilaterally, so Trump will be protected. No one will be able to say he incited anything.
Meanwhile, who looks like a dictator? Who has troops and barbed wire surrounding them to protect them from the people who supposedly love them? It’s called taking control of the narrative. Optics are important.
So right.
He’s always trying not to let the media narrative overwhelm people and by and large he has BEEN SUCCESSFUL…which is exactly why the MSM is doubling down on him, even when he’s left office…at least for now.
Despite all the trash talk, people still support him overwhelmingly and they know it.
He has given them a long rope.
Why don’t we the American people sue to get to the bottom of this? We have government suing government and if anyone has standing it would be us as a class action suit
This!
I said the same thing. Can’t we file a class action law suit from We the People? Demanding impeachment of Biden and Harris and Pelosi for treason?
Yes!
100% is there an attorney who would file it?
Dr Shiva in MA was running for a Senate seat and list. He won all the counties where the ballots were the old paper ballots. He found fraud in the other counties, tried to get a lawyer to take his case. Not one lawyer would take up the fight. He educated himself and presented his cases and both have been accepted by the courts. Dr Shiva also found out the voting machines are set to get rid of ballot images and many states do not keep the ballot images for the 22 months per Federal Election laws. Please refer to Dr Shiva’s website, videos, etc because I am just quickly writing this and I am not Dr Shiva.
Anyways, where could we get a lawyer with the guts to take this election fraud on? Dr Shiva says lawyers aren’t needed.
That’s a new and interesting idea. My thought has always been to bypass the politicians altogether. The Deep State actors are almost all in the upper echelon. “We the People” are not part of it. Yes, many are brainwashed by the MSM, but if the general public was made privvy to all of the evidence, I believe enough would rise up and demand a fair election or a reversal.
It is my belief that if the evidence were made public in many ways all at one time, it would spread so fast that 80% of the population would be aware in less than 5 days.
And need I say that the Deep State is involved in much worse crimes than election fraud? Many of you know what I mean by that. So when I speak of sharing all evidence, I mean the entire boatload. Perhaps that is too cryptic, but those in the know are aware of my meaning.
Thank you Patrick. My gratitude for your hard work and the work of other gifted patriots has no bounds. You are a warrior/Renaissance man. Thank you. Thank you. Thank you.
This is so disappointing. All this evidence of voter fraud and we have Biden in the White House. I sure hope this is still being looked into by the military. What can we do? Can we sue Congress for not representing we the people by at least looking at the evidence?
What amazes me is the sophistication and coordination, coupled with the high level of ineptitude.
It is like they preformed a “Mission Impossible” and everyone dropped their parking tickets as they left their station.
On top of all of this there are a few very smart people saying “Can you believe we pulled this off and got away with it considering all these idiots we had to work with”
Remember when Mr Gorbachov tore down the wall and the USSR fell with it. I was happy for the Russian people. Now they can have freedom and democracy like we do in the US I thought.
Well it didn’t happen because the people of Russia are just like many in the US. They are afraid of freedom or not willing to do the hard work it takes to keep it. The things Patrick & Co exposes are too difficult to think about. “Just take care of me Washington deep state and don’t make me think.”
“We put together I think the most extensive and inclusive voter fraud organization in the history of American politics.” – Joe Biden
That’s great Joe. Just send me my check when you get to the WH and don’t forget to mail me some ballots next election.
Thank you Mr. Byrnes. What is so astonishing to me, is the majority of citizens insist on believing the media and call this out as conspiracy. Just the high error rate and manual adjudication is enough fraud to thoroughly audit this election. The evidence is overwhelming. President Trump had poor representation, as well as, the threat from BLM/Antifa of starting a civil war. (BLM being nominated for Nobel Peace is like Saturday night Live) This election is done. We must now join together, and use our Constitutional rights to correct this travesty. The states should call for a Constitutional Convention, and agree on replacing our election system, and take the power away from DC on a number of issues. The power belongs to the people, not Washington.
The Blue States would attempt to use it to codify their theft. If they couldn’t, they would simply not participate.
Be careful of what you ask for. I fear an opening of the constitution in that manner would allow the blue states to codify many of the very things they are after. No, our constitution is not all that bad right now. Just enforce the laws as they are written.
I will make one exception to that comment. The 17th amendment needs to GO! The founders were very wise when they set the senate to be appointed by the states. It makes them essentially term limited because each now state administration would appoint a new set of senators to do their bidding. ANd it makes on e house of congress that is beholding to their respective states. Allowing them to be elected directly makes each of them essentially a “miniature president” with far-reaching powers, and no term limits in addition to their 6-year terms.
Hope everyone Dominion is suing sees this.
FWIW, the “fact check” makes an issue of UBS Securities Co., LLC. being the UBS New York affiliate, not the UBS Securities Co., Ltd. that is openly affiliated with the Chinese communist.
It should be noted that UBS Securities Co., LLC. had a whole lot of connections to the PRC anyway.
https://billlawrenceonline.com/china-bought-dominion/
It was noted that there were 3 Chinese board members of UBS NY, and two of them were also executives of UBS Securities formally UBS Beijing
Realistically, the only way President Trump (I love saying that!!) could prove there was fraud was to NOT win the election. Had he won the election, then the Deep State could say he was the one who cheated. If he lost, only then would make sense for him to present the evidence of cheating.
For those asking why we don’t get to the bottom of this, the problem is the courts – even the Supreme Court. None of them want to allow evidence to be presented. They are hesitant to get involved, but more likely, they don’t want to be the ones who will be expected to put their thumb on the scale in future elections.
That is likely why President Trump wants to bring this into the Senate – it puts the onus on the senators to hear the evidence, PLUS they are the highest state officials that can provide leverage to make the changes in their states. Failure to do that will get them primaried in their next election bid.
if that is Trump’s plan to win back WH, it is quite a long shot. I seem to lean toward the thought that he wants to use his loss to completely expose the swamp creatures and use his popularity to support the next person to carry out his ideology. Doing that he will not be attacked afterward by the Left and MSM and still can promoting MAGA doctrine! JMHO.
Ultimately, the only person who can answer is Trump himself!
can you pls stop freaking imagining what trump wants to do. expose this expose that. the guy blew it and did so because he WAS in ways a part of the swamp.
we got biden BECAUSE he didnt act when he had a chance to. the only thing we can do now is eensure that our elections are fair again. so that we have an immediate response when they stop counting votes/put pizza boxes to prevent observers, etc…
To really tell the story of this election will take a couple of novels. I suggest the interested people here on Patrick’s blog crowd source this history project. I would be happy to lend what time I can spare to contribute.
Here is a proposed list of topics that need to be investigated, please feel free to add, subtract or contribute.
1. Patrick has done a good job of providing much of the how the computer hack was done. I further break this down:
A. Each county involved, along with a detail to the best of our knowledge exactly what and when and how they did this. Much of this is already published but should be put together for each place.
B. Tracing of the evolution of the software, both in ownership and use. This should probably be done for each company and all the hardware and software.
C. A list of the known compromises, like solar winds and the malware found on servers. Where they trace back to.
D. A list of names of people involved, from owners down to who’s hands were on what keyboards. Then this should be further developed to a names database of all persons who helped both before and after. You could easily start with the 54 former intelligence professionals who signed the letter saying the Hunter Biden laptop was Russian disinformation. A Wikipedia of evil with lots of backup..
2. Voters. If they were going to create and/or switch a bunch of votes they had to have “names” to put on the ballots. How was this done? One way was a great deep dive into names some data analysis did that proved they latterly created fake voters. How are there 100 voters with the last name “Williams” who are all 28 years old in GA. In every other age group with the last name “williams” there are 3 or 4 voters. This pattern repeats again and again in the 6 counties that stopped voting. Ballot harvesting, there have been people going to jail for this but there is a lot of evidence that there were 100’s if not 1000’s of these harvesters working around the country. All the people who were told they voted early when they went to the polls. All the dead people and all the people who voted in two states after moving. All of these topics need further investigation and details.
3. Fake ballots, how they got them. How they filled them out when needed. All the strange things the happened around ballots.
4. State officials: Why is the “republican” board of elections of AZ not allowing an audit of the paper ballots? Why is this not happening in all 6 states in question? We know the names of each and every state official who are blocking audits. We know all of the officials and members of state legislator who pushed to change the voting rules. We know every judge who refused to look at the evidence. We need a list of all of them with connections. We need an investigation into each and everyone to see how and when they became compromised.
5. DOJ and FBI and DHS. A list of everyone who did nothing or actively blocked investigations. Find out how and when each and every one of them was compromised.
6. Social Media: Not just Jack and Jeff and other CEOs, we need board members and all “C” level executives and large investors. We need to know everyone of them and their connections and when and how they became compromised.
7. MSM: Names, Names, Name. We need to know everyone of them and their connections and when and how they became compromised. All of them from the street reporter to the board members. They are dirty and need exposure.
8. One part that is not talked about is how did they get all the workers, in each counting station to go along with this? Or enough of them to get around the honest ones? I have been doing some investigation and I think I know how they recruited the numbers they need. I will be working on this aspect of the steal either way.
9. ….
10. ….
11. ….
12. ….
If each person would work on just one person or piece of this history we could put it all together.
If we can get this into a working project I will pin it to the Inter Planetary File System so that it can never be censored.
I am not sophisticated enough to create a web site for this but I would gladly lend one of my domains for a place to host. This type of collaboration can also be accomplished with github.com. I again cannot set it up but would lend my github site to this project.
They have exposed themselves, now we need to put a spot light on each and every one of them. An NEVER let them hide an infiltrate again!!!!
We are the dragon awoken, and we can hunt them down one by one and burn them with the intense light of transparency…
If you are as FKN* mad as I am then take out you digital pen and start slaying all of them one by one, make the weak ones turn and expose the others.
Action worth tons of talk!
Feel free to help https://github.com/Deadheded/Crowdsource.2020.Election.History
I want to help. I’ve followed as much as I can get my hands on to read. What Patrick has done is opening the window into the Big Steal. I’m am so grateful to him and all of you who want so desperately to expose this for the world to see. We cannot give up. If there’s anything I can do, please reach out to me. I can help make lists and contact people.
Make a free github account (all the dolphin speakers have one) and join in. Pick a subject and start filling in the details.
Did Patrick say where the log of internet traffic comes from? I cannot imagine how that could have been made.
Is Sidney focusing on fixing the election rather than to have President Trump declared the winner? She’s an amazing attorney I am not, but just my 2 cents worth, maybe focusing on the evidence of fraud to be looked at gives the courts an out that they are not deciding the election just verifying the votes. Not sure if the 2 can be separated but 80 (minimum) million patriots need that verification what is holding these courts back from looking at it at least, for the sake of a functioning democracy going forward
Great article. However, it changes/changed nothing.
I’m more than upset that our beloved President took almost no action to out the fraud. That makes me wonder whether or not he is in on the plot to destroy America and it’s freedom.
Jovan Pulitzer put it best- see his videos. Had this NOT happened the way it is happening, it would not have been revealed. In fact, they could have just said “my bad” and then spent four more years perfecting it to a point we wouldn’t even have a clue that it happened.
In addition, there are still many who are in hiding and have yet to be revealed. Trump seems to be patient to let them reveal themselves. I have to give him credit, because I am impatient, and would have stomped on the bug as you seem anxious to do. Amazingly, EVERY DAY another piece of the puzzle reveals itself.
Let’s see how this all plays out.
He’s had multiple threats on his life. He may be concerned about the lives of his family as well. It could be blackmail.
Looking at this and basically it doesn’t add up…
Just bc parts or servers are stored overseas, it doesn’t mean that company interfered in the election. Don’t get me wrong, it’s incredibly stupid, but it doesn’t show that Germany switched votes, or Barbados, China etc. Also, if there was so much evidence, I think Trump would have acted. Period. He would never have sat on a mountain of evidence and done nothing.
The point here is, all election data should not be sent, transfer to any location by any means. It is against the law. But it truly has been, not even one but so many locations outside the US. The question is why the voting machines were connected to the internet? Just for the fun of it or the sake of sophistication of technology?
I believe that will be the basis for military intervention and arrests. Gen. Flynn had mentioned 30 days. Did he mean 30 days from his Tweet (or was it his interview? I forgot) on Dec. 31 or did he mean from Inauguration Day?
Patrick, As a senior military officer I often hear praises from the public regarding my service to country. I’m sometimes embarrassed by their praises because I volunteered my service to a worthy cause, liberty as documented in our founding docs. That said, I’m/we are the ones who should be thanking you for your service to country. You don’t need to wear a uniform to support the just cause of freedom. I’ve been reading your DeepCapture site and I’m thoroughly impressed by your rare intelligence. I only wish I could be a thinker in that same space! I don’t want to waste your time. You have important work to do. I wish I could be of assistance and I would do whatever is needed to further your cause to make rational sense out of the Big Steal, which is what this election was. If you sense a bit of anger you’re sensing correctly! And, I would approach any work for you with that same intensity of controlled anger. I’ll leave this post and say one thing…. thank you from the bottom of my heart for taking a stand and showing the world what we’re up against – the global subjugation of individuals who are blindly walking into their new status – subjects. Keep charging. There is great love you out here in the barn! Four legs good, two legs better!
Charles, make it thousands more for us out here who want to defend our republic and way of life here in the US!
Perhaps there is something far worse than the fraudulent election? Just what did the SolarWinds hack compromise? Why the need for the expanded and continued Military Show in DC? Why the In-Your-Face RICO type bans on free speech? And why did most offices and branches of government, sworn to protect the Constitution, stand down? Again, what could be worse than our hacked election?
If the claims being made are true, it is important enough to make the case in a clear, organized and coherent manner. And correct grammar might make it more credible. If it is not worth the time and effort to make it clear, it will be assumed that Patrick is a quack.
David, use your brain if you have any. As Patrick said in the beginning, he is publishing the draft version as soon as he can because the story is too important to wait until a polished version is ready.
Question; the Dominion lawsuit against Sidney Powell. Would this be an avenue to get this information out in the public? Not an attorney. Just hopeful that this gets out. And please, keep Rudy away from this
Michael, what Dominion is doing is a typical leftist move. Powell has a lot of the goods on Dominion, so in typical leftist fashion, Dominion turns around and tries to sue her for liable. I’ve watched that move happen multiple times over the past four years in one or another blue state when it didn’t like what
THE President was doing. Just a lot of huffing and puffing and saber rattling on their
part.
Bottom line – where does this leave THE President now? How do we remove the imposter from the White House? Who is going to listen to the evidence in a court of
“law”? The imposter (and his ilk) is rapidly tearing our country apart from within and needs to be stopped immediately. Will the military stop and remove him? What’s next, if anything??
I thank Patrick for his succinct display of the evidence and hope he will also tie up some loose ends next. But, where do we go from here? Thus far, it appears Trump’s September EO was for naught.
Patrick – you are an incredibly brave person and your writings, although shocking, ring true and help explain so much. Those of us who still seek the truth, hungrily read everything we can find to try and understand our country’s devolution toward Biden’s inauguration. But, we’ve been strategically demonized & forced into the shadows for seeking to quell/ understand/move beyond this crest fallen feeling of disillusion and faith in our touchstones of liberty and equality. We use fake names. We are careful what we post. Please be careful; there likely are many people who have been coerced or are simply too afraid to take action or speak out. I used to say “this too shall pass” but I have no trust this time that it will.
So, now what? If this is true, are you signaling that there is not one honest judge, whistleblower, or DOJ individual who would come forward and save the country? If I had seen something up close & personal, I would sacrifice my life for the USA. I hope & pray you are not trying to sell a Tom Clancy novel or get a contract for spy movie.
I remain confused and deeply concerned. This shouldn’t be a political issue. This is a national security issue and our military should have immediately interceded. We are a superpower with a nuclear arsenal and our voting systems (critical infrastructure) have been compromised. This is also a global security threat and the world is silent. Why? What happens when these foreign adversaries demand payback from the current administration? What if this payback is more than just relaxed trade policies and involves a military strike? Whether or not the current administration was aware of the foreign assistance- the leverage alone is too much to not be deemed a credible threat to our national interests. I also cannot reconcile why the POTUS allowed the GA runoff on these compromised machines, handing over control of the Senate to a party who benefited from foreign interference by our adversaries, removing a critical layer of checks and balances. Why did the military allow this [1/5 election] as well? There are huge pieces of this puzzle that are not fitting and major questions that need to be answered. This should have been brought out to the public Nov 3 and in the days following. The President had a press secretary and could hold daily briefings as he did with Coronavirus. Why was this not done? Something is very off about all of this. (I’m not insinuating what you’ve provided is not factual. I am asking the questions no one else seems to be.)
Yes, I can’t agree more! I have been asking these questions. Why isn’t our military getting
Involved? This was foreign interference in our election! It should be an act of war.
What is happening (or not happening) is not making sense! It seems like the message with the new Super PAC is to “get involved on the local level”. I feel like we just handed our Country over to the CCP and only a few brave Patriots like Patrick are doing anything about it!
Patrick, thanks for all you’re doing. Waiting on the full reveal.
According to US Law: “Fraud vitiates everything”. Wouldn’t it be remarkable if this second farcical “impeachment” becomes the means to prove the fraud? Trump can call any witnesses he wants and take as long as he wants. Once a “trial” begins, the Senate cannot do anything to stop him in his defense and can not take up any other business till it’s end. It’s already unconstitutional if for NO other reason, Roberts won’t sit as Judge. The Constitution clearly states that the Chief Justice is the only one who can. The Senate Pro Tem has no authority to hold a “trial”.
I sincerely doubt any evidence will be allowed. I think even the murder turtle just wants to get this over with. They know the out come (perhaps)- a little on that next paragraph. Th idiot they appointed to run this will call foul on any evidence – despite its relevance to the charges. SO, I wouldn’t hold my breath on that. Yes, I hope like you do.
Now- about that 55-45 vote. Do not be surprised if there are MORE republican TDS votes than in that vote about the constitutionality. Those RINO’s were allowed to vote against constitutionality because they all knew that the democrats had enough votes to toss the measure. At least Rand Paul was able to reveal a handful of them. I wouldn’t be surprised if McConnell has been working some back-room deal with RINO’s and Schumer for some promise of power sharing. He is likely hoping he can coerce enough votes to actually force impeachment- he has as much as admitted it.
This would also explain Trump’s patience in making any sort of move until after their charade is ended. More traitors may be revealed at that point. I fully expect McConnell to vote in favor of impeachment.
I worry that if Trump’s team tries to offer evidence of election fraud at the impeachment trial on live TV, there will be another false flag like when Repubs offered evidence during the vote certification hearing when a ‘spontaneous’ Capitol riot diversion happened. Stay away from skyscrapers and large trucks parked in front of them. I fear a 9/11 type event blamed on ‘domestic terrorists’ and used as an excuse to black out all media coverage and round up ‘the usual suspects.’
The declaration states:
“4. Dominion Voting Systems is owned and controlled by foreign entities. We lose control of the data when it goes to a foreign country. For example:”
With one of the servers being in Frankfurt:
“• http://www.scytl.com with IP 52.57.209.147 (ASN Range: 52.57.0.0/16) is (was) located in Frankfurt Germany”
What is the current status of the Frankfurt server? IMO, should be the key to showing what data manipulation took place after the Dominion systems running our election supposedly sent election data to them.
If the stories about the gunfight and loss of life to secure the Frankfurt SCYTL server, and it supposedly showing that Trump won the electoral college count by 410 to 128(?) are true, why hasn’t that evidence been validated and revealed?
Don’t know what to believe anymore. My fear is that Biden/Harris and their goons are burying everything as fast and as deep as they can. Hopefully, under some watchful eyes… 🙂
It’s bewildering and perplexing that Patrick and his team had to do the work of the DOJ & CISA. Where is Krebs now, I wonder. Paid off? He didn’t even seem to have the credentials to be in that position. A degree in environmental science? Come on, man.
People ask why Trump did not activate the 2018 Executive Order or take other action to correct the election fraud.
If you review his life work, Trump is a negotiator and conciliator by nature, not a fighter,although he wanted to project that image.
He never served in the military, and his political career until 2015 was erratic.
He never took any punitive measures against his political opponents while President,and preferred compromise on foreign disputed after a noisy start;eg North Korea,Mexico,European Union.
Bottom line; Trump was not emotionally capable of having a street fight over the elections, being satisfied to just having protests about the Steal.
Hardly anyone thinks Trump is a Globalist in sheep’s clothing. Why not listening AND actioning? – would explain a lot !
Dominion was operating BEFORE 2016 elections so who can honestly say DJT “couldn’t have been ‘artfully’ sELECTED to divide ?
Rothschilds bailed him out from MASSIVE debt waaay back when. No allegiances there ?
Masses are EASILY deceived and led astray by orche$trated dividing. A LOT of that is, was and will continue to be going on. Meanwhile … this is USEFUL :
*DILUTED, water-soluable, Chlorine-dioxide GAS is NOT “laundry bleach.”
Enjoy these affordable TRUTHS.
Bolivia’s CV19 death-rate went from 100/day (and climbing) down to ZERO-range across their entire nation using an inexpensive, NON-rushed, NON-vaccine, science-based, APPLIED research ! HOW ? !!!
Diluted! CDS gas-in-water WORKS for CV19 … and MUCH more !
https://lbry.tv/@Kalcker:7/Why-ClO2-works-against-covid-19:2?r=3HjkA7vfUjLE4gTappooSekm2PuYr5Du
LEARN w/ an E-Z CDS home-prep VIDEO
( 1st select language at the top )
https://andreaskalcker.com/en/index.php?option=com_sppagebuilder&view=page&id=137&Itemid=735
Re-search “AndreasKalcker.com” –
Int’l Biophysicist / Humanitarian
Find CDS kits at:
https://kvlab.com/chlorine-dioxide-products/
www.lvwg.org
( choose your language @ the top )
Book: “Forbidden Health … incurable was yesterday”
Its GREAT-CONTENT .pdf is here :
https://voedia.com/en/inicio/26-forbidden-health.html
… worth every penny !
… chlorine dioxide GAS-in-water ALSO cures malaria in 1-2 days !
The ‘problem’ is that the pharmaceutical [peopled] industry can’t patent it for their profit.
… the pharmaceutical industry sells over ten billion US dollars in malaria prophylactics each year.
“King Arthur: Look, you stupid bastard, you’ve got no arms left!
Black Knight: Yes I have.
King Arthur: Look!
Black Knight: Just a flesh wound.”
– Holy Grail
“Please sir, I want some more.”
…
MOAR?? He asked for more after eating his supper??”
– Oliver
One would think that this article would have been more than enough to continue Trump’s rightful place in the WH.
Nope! it is not just about Trump anymore because it has become a serious issue regarding our election systems. If not find out the truth, we are no longer having a free and fair election!
For those asking the tough questions like, why hasn’t the evidence been shown yet and why didn’t the WH press Secretary just hold press conferences regarding the evidence if they had it…. let me just share what my research and following of those I’ve discerned to be “truth sharers,” of which Patrick Byrne is one, has shown me. First of all, understand fully that this evidence, once shared in entirety, is of such a damming nature GLOBALLY to not only ours, but foreign governments, that there must first come a time when it can be shared publicly with (hopefully) minor fallout in the way of bringing forth civil revolutionary war. We simply are not there yet, we were not there in November, December, or January. I’ve been following and a lot of the evidence actually has been shared but not many were watching. Of those that were, it did not include the media, actually the media refused to cover it… even when the WH press Secretary showed up with physical affidavits in hand to present to the world, media (Fox included) refused to play it! The full extent to which this corruption runs is so deep and intertwined into every aspect of the world we live in that bringing forth justice in one matter forces justice to be brought in all matters, including corporate America, wall-street, most 3 letter government agencies, banking systems, educational institutions and content, human trafficking, Hollywood, politicians, judges, and even religion. It will bring forth first a breakdown of current systems then be followed by a great rebuilding of just about everything from the banking system to schooling to government to the church. The scope is huge. It’s not just election fraud or who sits in the Oval Office. It’s good vs. evil and only God can fix it, in His way, on His time. Pray, guard your hearts and your minds, and if you don’t know Jesus, get to know Him. Repent of your sins and ask Jesus to come into your heart. We gotta give this world back to God….
That sounds like a very cheap excuse for not giving us the “real” evidence.
Especially since Byrne is already implying foreign countries like Italy, China, Iran … So why bother now?
It sounds more like a leader of a cult who promises paradise in some distant future.
You are correct Jessica, only God can fix it. It is too big for man. We must first come to that realization.
All these “systems” are so corrupted they basically cannot be repaired. God often must tear-down (first) in order to build up and these systems are useless if they are not built on a firm foundation.
Now if you knew this (ie. that these systems were broken beyond repair and nothing you could do would change that) would you be spending a lot of effort repairing it? I think this is what no one is apparently seeing (or perhaps it only comes with spiritual discernment). I think putting Rudy on the job was just to make it look like they were attempting (in every possible way) to challenge things legally when we all knew it was futile really (and another plan was really already in place to fix this election fraud issue along with ALL the other issues we have). Think bigger than just the election fraud. If we fixed that issue alone we would still have many, many more issues needing fixed.
The whole system (or web of systems) must be replaced. I believe that is what has been happening over the last 4 plus years (unbeknownst to those not watching or watching but not seeing).
DJT is a genius builder and perfect for the job. Anyone who thinks he has walked away or somehow abandoned us is STILL ASLEEP!!! Wake Up!!!
It is these people who are abandoning DJT NOT the other way around! They just apparently have so little faith or spiritual discernment they attack others (including DJT) for their own responsibility in this spirit of stupid that has come over them and much of this nation.
Use the time we are in now to come to Christ (repent and give you life to Him) and concentrate on developing an honest relationship with Him. We are going to have a lot of work to do to fix our nation and will need the strength, direction and perseverance only God can give us. So if you need to feel like you are doing something positive, seek Him!
Soon you will see that all this had to work this way (and it probably always had to be the military since the systems are all way too corrupt to expect any outcome to be fair or legal-the enemy has spent too many years infiltrating everywhere). We are to use what we are learning right now as far as the fraud and corruption etc to help build a firm foundation for a new America that IS equitable and fair. But the foundation cannot be built without God in the equation, or again it will be destined to fail.
Unless the LORD builds a house, They who build it labor in vain; Unless the LORD guards a city, The watchman stays awake in vain. Psalm 127:1
My problem in all of this is IF THEY GOT AWAY WITH IT THIS TIME….. IT IS NEVER GOING TO STOP…. The DEMOCRATS NEVER get better! Only WORSE. We have complete CRIMINALS and SICKOS RULING OVER US and I just want off this plant. The fact we just have to “live with it” and “try again” is a JOKE
Thank you, Patrick! Stay safe.
Word was DJT would start working on an election integrity project. With the House Minority Leader meeting with him I am concerned he is getting sucked into the swamp again. This unholy alliance will be a distraction to the important work of reconstituting a free and fair election and a final blow to the Republic.
My conclusion to this whole election saga is that the deep state has total control. The evidence to support, at least massive investigations and court hearings has been all laid out for months yet it’s ignored. The American govt is a uniparty system at the positions that actually matter.
Patrick,
If the power belongs to the people, why is Trump telling us to stand down? Wasn’t the purpose of the second amendment to overthrow a tyrannical government? President Trump kept popping up telling us that violent people didn’t belong in his movement and that the “best is yet to come.” That tells me he has a future plan, one that is playing out right now in Florida with his “office of the former President.” Obviously, the next move of the DS is going to be taking our guns because without them, you cannot remove a tyrannical government and that is exactly what this government is. We are obviously at a point in our country where we either have to make a move or let them move in on us. You can either put all of your faith in Trump and pray that he has a plan to take these people out or it’s up to We The People. What do we choose?
Pence dropped the ball plain and simple. He lacked the courage and was not principled. Our state and federal election officials are responsible to conduct fair and secure elections and they were criminally fraudulent or negligent. There was more than enough evidence for him to send the electors packing and have the states re-run their elections fairly and securely. New elections would have exposed the fraud. Pence was the last solid chance to keep the election respectable. Unfortunately, the precedent has now been set…unfairly, to our pain and suffering.
Pence wanted Trump out from the 2016 election line up. He and Others has it all planned out. Look who he had as his immediate staffers. Koch Brothers placements. No Pence is a POS and needs to hang for treason.
Here’s my problem with your article… Just based on Executive Orders written and the dates of the orders, I am calling BS on the fact that “poor Trump was left in the dark” and is being blindly lead by clowns. He has a plan, and I believe you are angry that the plan doesn’t involve your hard work in obtaining this evidence. I strongly believe there is a bigger picture, there is MORE that will be exposed that just election fraud. Foreign interference is not limited to elections either.
Please keep going but think logically in regards to what Trump knew and didn’t know. Just look at his EO’s.
I agree, the executive orders are the key; we have been under a national emergency since Trump signed the September 2018 order; there’s a reason; that order was written for exactly what happened, it was preplanned; there’s a reason; I just don’t know what it is; I use my own discernment, it hasn’t failed me yet; Trump laid down, he’s laying low; his family is laying low; there’s a reason; all I can do is listen to Jeffrey’s explanation, he’s not a conspiracy theorist, he tells it like it is; we share that discernment, discerners do not abound in their own circles, and they always find one another.
Does anyone know what ITAR means?
Does anyone have rational explanation from Edison Research/Scytl/NYT JSON datafile that so many mathematicians have torn to pieces?
I have been monitoring the internet for a valid debunking of the now famous JSON data files and I have yet to see a logical explanation for the devastating mathematical implications found within the data. I’ve seen Edison and Scytl responses that say they created no such *report* put they do not dispute the data. For those who have seen the data, they know the JSON data displays like plain text. Many have converted the data to Excel spreadsheet form and that is the only basis for Edison/Scytl disavow if you can call it that. The bottom line is if this data “is what it is” there should be nothing else required to establish undeniable fraud as the data clearly shows impossibilities in the data. Specifically and most convincingly is the repeating and shuffling ratio analysis performed by Edward Solomon using Euler’s totient function. Can anyone add to this?
No there is not, just people saying it is not good data without any explanation. Seems pretty obvious that the only way to have those data “errors” is through intentional human intervention. Funny how all of them are for Biden, not one of the “errors” in this suspect data is for Trump.
TrackJ won’t explain that one either.
Concerning the NYT .json feed, I think it’s important for people to understand that the negative vote changes are human errors. There is a good example of an explanation here:
https://www.usatoday.com/story/news/factcheck/2021/01/06/fact-check-changes-georgia-vote-totals-due-reporting-errors/6562978002/
What you learn in that article is that Edison in not hooked up to the tabulation machines in the states. They actually have to talk to people/reporters to get the current state of the count and enter it manually into spreadsheets. So there’s plenty of room for human error.
Also, even more importantly, the states don’t certify Edison’s vote count that people analyse in those .json files. The states certify THEIR OWN tabulation result. Edison only reports the current state of tabulation. So if a leftist Edison call center worker decides to delete 100.000 Trump votes in their spreadsheet, it has exactly zero effect on the tabulation of the state. What happens is that Edison’s report is now 100.000 votes of, which they will notice sooner or later.
You see negative vote changes in many states, even those without Dominion machines. And no, the changes are not always for Biden, that’s just incorrect. They might be on average because call center workers are more likely to hear a Trump vote total wrong or something. I don’t care.
Byrne should upload reliable precinct level data for us and tell us in which precincts exactly votes were switched.
I responded at length to this earlier but I don’t see it posted so I’ll try again. Sorry if this ends up being a duplicate.
The voter integrity group has stated that the Edison Research JSON file is not a product of human tabulation, rather from the time the results (updates) are transmitted it is all electronic. There are no humans involved. Makes sense if you think about it. The JSON file is down to the precinct level for reporting. Edison Research has an employee at every single precinct? That person then makes a phone call every few minutes to a ER call center to manually give new counts? Uh..that sounds incredible. See Georgia Senate hearing @ 4:39 Data Integrity Group explanation: https://www.youtube.com/watch?v=u5ZP_HpBKos&t=16723s
But…Let’s assume for the sake of discussion that the counts were entirely relayed by humans and recorded manually across literally thousands of precincts. Identical ratios appeared simultaneously in several precincts on the same time stamp. The same exact ratio stopped simultaneously in those precincts only to begin again in different precincts with again the same exact ratio. The data is not mathematically possible in a naturally occurring data set. It was demonstrated using Euler’s totient function that the probability is less than 1 in 10 to the 49th power which is less than 1 in the total number of atoms in the observable universe. See Edward Solomon’s analysis: https://rumble.com/vcye71-edward-solomon-math-proof.html and here https://www.youtube.com/watch?v=O1cCRYOesWc&t=370s
Please show me the same negative votes for Trump. I have looked over GA and PA and they all go Biden’s way.
Why do you even keep focusing on these files? As I have pointed out, they are from Edison. You should focus on data from Scytl.
Show me, for example, where in Scytl’s data for Georgia 28966 votes were deleted and I change my mind.
Also, if you still don’t believe me that Edison’s feed is useless, compare the feed of Georgia’s presidential race to the senate race:
https://static01.nyt.com/elections-assets/2020/data/api/2020-11-03/race-page/georgia/senate.json
The large vote reduction of -28966 in the presidential race isn’t there. What happened? Did they forget to delete senate race votes? These reductions are meaningless, this is not the data from the tabulation machines.
Do yourself a favor and don’t spend your time looking over and over again at meaningless data. Look at Scytl’s data and try to substantiate your claims with it. You all should ask Byrne for the data, he should provide it to you. Since some of his plots use precinct level data, he has it and should make it accessible to all of us.
In a case submitted to the supreme court, an intelligence officer lays out how information is transmitted via dominion, Scytl and Edison Research. The declaration begins on page 285. Someone is lying, that’s for sure.
https://www.supremecourt.gov/DocketPDF/20/20-859/164740/20201224101037520_WI%20Appendix.pdf
If you ctrl F Scytl and Edison research you are going to find copious amounts of data on both. Much of it is backed up with electronic analysis. Much of it is extremely concerning and should be fully investigated.
I don’t accept for one second the idea that the JSON files are produced from thousands of ER employees on the ground in precincts giving phone call updates to a call center. But let’s suppose they were, how then do you get the exact ratio in counts in many precincts starting and stopping on the exact time stamp and then re-surfacing in other precincts on the following time stamp? The odds of that are impossible. Ed Solomon put the odds at less than 1 in all the atoms in the observable universe.
@Blank:
There are two related things in the lawsuit:
A statistical analysis and the analysis by Spider.
Statistical analysis: For some parts of the analysis they seem to use Edison data, which is, as I have now pointed out multiple times, complete BS. Further, they don’t seem to know themselves where they got their data from:
‘We perform a precinct level analysis of Fulton and DeKalb counties in Georgia based on an aggregate data set likely culled from the New York Times.’
‘likely’? Are you kidding me? What kind of a scientist analyses data without knowing what he’s analysing exactly?
This analysis is untrustworthy.
B) Concerning the analysis by Spider:
That guys background has been ‘debunked’:
https://www.businessinsider.com/sidney-powells-secret-source-spider-is-actually-an-it-consultant-2020-12
I don’t see why we should trust anyone who is lying about his background. It’s not worth my time.
—-
And to Ed Solomon: It’s literally always the same with those people. They find some person who is an ‘alleged’ expert showing you a spreadsheet with some numbers on it telling you it is ‘astronomically unlikely that this happens’. And since they say he is a mathematician what he’s claiming must be true.
Is it so hard to tell
– what data exactly he is analysing (SOURCES!)
– what analysis exactly he performed on the data including all assumptions he made
– what his conclusions are (in a structured manner)
???
These videos are literally all the same. These people are doing this for month now. It’s unfounded gibberish. So you can ignore it basically.
————-
Since Byrne is not able or inclined to give the people here some data sources to corroborate these claims, I will give you a link to some Scytl data and scripts to scrape it yourselves, so that everybody can reproduce it. You can then compare this data to Edison’s data and see that
a) The observed vote switches are only in the Edison source, representing corrections by human beings
b) there are no other vote-switches to be found in the Scytl data.
I’ll do that as fast as I can. Will take me a few days.
Just to get this out of the way, I do believe there was industrial scale software-assisted electoral fraud.
That said, please be wary of any analysis based on Edison data feeds if they are 3-digit percentages rather than raw vote counts. 3 digits of percentage may not be enough significant digits to recover the raw vote totals. The computed totals are truncated and can result in what appear to be vote swapping. These two links explain what happens.
https://securitydebrief.com/2020/11/14/seeming-discrepancies-in-voter-data-fuel-for-disinformation/
https://www.metabunk.org/threads/claims-of-irregularities-in-nyts-edison-election-data.11450/
Mr Byrne, many thanks for your commitment to our country. Easy question, can and will this overturn the stolen election?? If Pres. Trump is not put back in office within months,the system will remain a swamp. Thank you and await your response.
Yes. IF there is a way ala Reddit/GameStop to make this happen, it is probably the only thing that can return this new nation of the United States of Dominion back to the United States of America. However, with the 3 prong Marxist election control (HR 1, mandatory federal mail in voting, and millions of illegal alien voters), nothing may ever work.
Patrick – what do you think is going to turn up in Arizona now that they are going after the Dominion servers? Hopeful they will find something? And, I am guessing they are hiring the same firm that Antrim County did (it said texas based).
I hope they do, but I’m skeptical because the audit logs are not tamper-proof. I suspect what they will find are wiped audit logs (which is suspicion in and of itself, but at least the direct evidence is gone).
ASOG found evidence in Anterim county because the attacker failed to wipe all the logs. There was an untampered and intact error log that revealed the unrealistic level of scan errors. Ballots with scan errors go into the adjudication state. An election official with the right authorization level can batch adjudicate ballots (“These 1000 voters really meant Biden, so there … FIFY!”)
PROOF OF ELECTRONIC VOTER FRAUD
Scorecard Hammer program SWITCHING VOTES CAUGHT LIVE ON CNN!
SMOKING GUN: ELECTRONIC VOTE FRAUD CAUGHT LIVE ON CNN! #THEHAMMER #SCORECARD
https://www.bitchute.com/video/3PUpbMyrOtjF/
Thanks Patrick. Can’t wait for more chapters! I especially liked the Pam Bondi lines. Mendacity is a word That is seldom used in my world, yet fits perfectly in Trump warfare. Sorry to read about Giuliano’s drinking. This is a crippling disorder. Trump is wise to avoid it. So many in Washington are high function alcoholics.
Things that make you go MMMMMMMMMMMM?
Things that make you go MMMMMMMMM?
Thanks Patrick. Can’t wait for more chapters! I especially liked the Pam Bondi lines. Mendacity is a word That is seldom used in my world, yet fits perfectly in Trump warfare. Sorry to read about Giuliano’s drinking. This is a crippling disorder. Trump is wise to avoid it. So many in Washington are high function alcoholics.
Things that make you go MMMMMMMMMMMM?
People need to be aware that Media Matters Share/Blue trolls seem to be following the same script from 2016. Back then someone hacked into their website and managed to get a screen shot. It basically said to pretend to be Trump supporters and conservatives who were worried, concerned, disillusioned, etc. about Trump. The goal was and still is to separate Trump from his supporters.
I’m not claiming there might be a few genuine Trump people who are confused or angry. But not as many as you think based on comments here and other websites. Just keep this bit of info in the back of your mind as you read.
Patrick, I doubt many people will get the Milton Berle reference or even know who he was. Now I can’t erase the image from my mind!
I do… he’s supposed to have had an affair with Aimee Semple McPherson..Now try getting THAT out of your mind.
And just in case you don’t (I didn’t) here’s the reference without going into details here…..
https://www.reddit.com/r/todayilearned/comments/6wjq9s/til_milton_berle_considered_americas_first_tv/
Legislative Branch: corrupted and captured
Judicial Branch: corrupted and captured
Executive Branch: corrupted and captured
Armed Services (MIC pawns): corrupted and captured
Fourth Estate (Administrative State, SES, etc.): corrupted and captured
Media: corrupted and captured
Wall Street: corrupted and captured
Voting and Electoral System: corrupted and captured
Active Military and Veterans who will faithfully serve The Oath: UNCAPTURED
Largest armed civilian population on planet who will defend against all enemies foreign and domestic to protect God given freedom and liberty: UNCAPTURED
CUI BONO or For whose benefit?
18 USC SECTION 2381 TREASON
Whoever, owing allegiance to the United States, levies war against them or adheres to their enemies, giving them aid and comfort within the United States or elsewhere, is guilty of treason and shall suffer death, or shall be imprisoned not less than five years and fined under this title but not less than $10,000; and shall be incapable of holding any office under the United States.
18 USC SECTION 2384 SEDITIOUS CONSPIRACY
If two or more persons in any State or Territory, or in any place subject to the jurisdiction of the United States, conspire to overthrow, put down, or to destroy by force the Government of the United States, or to levy war against them, or to oppose by force the authority thereof, or by force to prevent, hinder, or delay the execution of any law of the United States, or by force to seize, take, or possess any property of the United States contrary to the authority thereof, they shall each be fined under this title or imprisoned not more than twenty years, or both.
18 USC SECTION 2385 ADVOCATING OVERTHROW OF GOVERNMENT
Whoever knowingly or willfully advocates, abets, advises, or teaches the duty, necessity, desirability, or propriety of overthrowing or destroying the government of the United States or the government of any State, Territory, District or Possession thereof, or the government of any political subdivision therein, by force or violence, or by the assassination of any officer of any such government;
or Whoever, with intent to cause the overthrow or destruction of any such government, prints, publishes, edits, issues, circulates, sells, distributes, or publicly displays any written or printed matter advocating, advising, or teaching the duty, necessity, desirability, or propriety of overthrowing or destroying any government in the United States by force or violence, or attempts to do so;
or Whoever organizes or helps or attempts to organize any society, group, or assembly of persons who teach, advocate, or encourage the overthrow or destruction of any such government by force or violence; or becomes or is a member of, or affiliates with, any such society, group, or assembly of persons, knowing the purposes thereof —
Shall be fined under this title or imprisoned not more than twenty years, or both, and shall be ineligible for employment by the United States or any department or agency thereof, for the five years next following his conviction. If two or more persons conspire to commit any offense named in this section, each shall be fined under this title or imprisoned not more than twenty years, or both, and shall be ineligible for employment by the United States or any department or agency thereof, for the five years next following his conviction. As used in this section, the terms “organizes” and “organize”, with respect to any society, group, or assembly of persons, include the recruiting of new members, the forming of new units, and the regrouping or expansion of existing clubs, classes, and other units of such society, group, or assembly of persons.
https://uscode.house.gov/view.xhtml?path=%2Fprelim%40title18%2Fpart1%2Fchapter115&edition=prelim
From what we hear a server in Belgrad, Serbia was involved. The NATO bombarded Yugoslavia 1999 (Operation Noble Anvil). There should be enough people on the ground in Serbia with motivation to help to bring some light into this mess.
Why haven’t we gone after this corruption? This action is an act of War against America and her People.
For all of you who like to work with the NYT .json data from Edison, there is an article you should read about the vote switches seen live on TV in the Georgia runoffs:
https://www.usatoday.com/story/news/factcheck/2021/01/06/fact-check-changes-georgia-vote-totals-due-reporting-errors/6562978002/
It’s important to understand that Edison, unlike many here believe, is not hooked up to the tabulation machines, so they don’t get election data directly from those machines. It seems like they actually have to talk to people working in those states to get the current result and enter the data MANUALLY into spreadsheets. So there’s plenty of room for human error.
What’s also important to understand is that states don’t certify Edison’s results, they certify their own tabulation results. Edison only reports or tries to report the current state of the vote count. So if an Edison reporter or call center worker deletes 100.000 votes in THEIR system it does not affect the states own vote count.
The only thing that happens is that Edison’s tabulation is now 100.000 votes off, which they will notice sooner or later and correct it.
“It seems like they actually have to talk to people working in those states to get the current result and enter the data MANUALLY into spreadsheets. ” again with the false and unsubstantiated statements.
“they certify their own tabulation results.” and again false statement not backed up by anything.
Edison gets data in a direct feed from Scytl. No one is on the phone and then entering that data by hand.
The central tabulation machines in each state are connected to Scytl, clarityelections’, servers. Those server’s maintain that data in 3 different databases. The states certify their election based on the vote counts in one of those 3 databases.
Well, I gave you an article with Edison’s own statements. Do you have sources for your claims? You are directly contradicting what Edison says:
‘a call center operator at Edison Research erroneously entered data from a reporter on the ground at the Bibb County Office’
What’s the basis for your claims?
Also, why should media outlets contract Edison, if they can get the data directly from Scytl instead? Seems pretty illogical.
Hmmm. I read another debunk that pretty much said the same thing. So what Edison is saying is that their reporting happens like this:
A human Edison Research employee is stationed at every county. The ER employee then at various intervals (time stamps) is updated with count updates from a human election worker. The ER employee then makes a phone call back to ER and informs another human in an ER call center who then enters the count into the ER feed. Further and inexplicably, if an error occurs as in the case of your cited example, the error is corrected again through the same human chain and then recalculated and entered into the feed. This would account for the decrments. I’m sorry, but this explanation is extremely unconvincing and only causes more eye brow raising.
First, I’ve read that this process is entirely human free. See Georgia state senate hearing starting at 4:39 where the analysis team from Data Integrity Group explains how the data is sent through the precinct/county/scytl/edison research chain of custody. https://www.youtube.com/watch?v=u5ZP_HpBKos
According to the Data Research Group, they used 4 separate data sources. (see above video). None of the human interactions occur in the way that ER describes. But lets pretend it happened exactly as ER describes. How is the error identified? Your USA Today citing says that in once instance a worker made a mistake between a 3 and an 8. The count went through incorrect. How was it then discovered minutes later for correction. If things happen as reported by USA Today the remote totals come in and become just a small part of the aggregate. And that’s what you see in the JSON files. Why would anyone at the county level be aware of the the incorrect reporting? Seems very strange and unlikely if not impossible. Second and more importantly, how would random human reporting in any instance result in precise ratios appearing simultaneously in certain precincts only to stop simultaneously and re-appear in different precincts on the very next time stamps. As I indicated in my comment above, this violates Euler’s totient function math principles. See Ed Solomon’s explanation. https://rumble.com/vcye71-edward-solomon-math-proof.html and here https://www.youtube.com/watch?v=O1cCRYOesWc&t=2s
If humans are reporting from the precinct level to other humans at ER, if is impossible for the ratio occurrences to happen unless the totals are being manipulated by an algorithm. It is literally impossible.
Just to get this out of the way, I do believe there was industrial scale software-assisted electoral fraud.
That said, please be wary of any analysis based on Edison JSON data feeds scraped from NYT. If the feed is expressed as 3-digit percentages rather than raw vote counts, then the analytical results are suspect. 3 digits of percentage may not be enough significant digits to recover the raw vote totals. The computed totals are truncated and can result in what appear to be vote swapping. These two links explain what happens.
https://securitydebrief.com/2020/11/14/seeming-discrepancies-in-voter-data-fuel-for-disinformation/
https://www.metabunk.org/threads/claims-of-irregularities-in-nyts-edison-election-data.11450/
Perhaps a video that presents all the evidence and testimony(including some of those who signed affidavits) to the public is needed ?
Perhaps a company like Voatz could run a public exhibition/test election with fictional candidates to prove the merit and integrity of their voting software?
With the current system none of us have any way to verify that our votes were accurately counted or even counted at all.
Truthfreedompeace: go to Duckduckgo.com (never use the evil Google which censures) and search for Antrim County dominion machine forensic report. You will find a report for one county for Nov 2020 election. Dominion Voting machines were used in 28 states in 2020 election. You can find tons of other evidence of voter fraud. Just do a search.
I have listened to all the Senate hearings in all the swing states in question. I heard all the testimonies, read all the court filings. I have been doing my own research on this matter everyday since November 4. I do agree with the evidence Patrick has provided and there is more evidence in which he has not shared. The problem is some people did vote for Joe. That part of the population is our opponent and sadly nothing will be done. We will just keep living in a fake Republic with a fake President and keep voting in our fake elections. If anything was to be done about it it would have been our beloved President. But sadly nothing was done. I will never understand why he did not use his executive order and take control of the situation. And because of that I feel a terrible sense of sadness and heartbreak that I’m afraid will be part of me everyday of my life. The once happy me who loved our country is sickened by what has become.
I feel your pain.
You can always watch re-runs of Three’s Company and take your mind off things …
I have been On a roller coaster ride these past couple of months. But this article has given me hope again. Thanks and god bless you.
I think the fraud was really with the mail-in ballots.
Things were done like registering homeless people in shelters. Which the same homeless people can be registered in other states as well.
Facebook’s Zuckerburg funded Center for Tech in Civic Life (CTCL) which paid local officials to increase voting.
See https://twitter.com/PhillDKline
I stumbled across your website today and am extremely thankful that I did. Keep the faith, darkest before the dawn and all that keeps me and others going.
“Hey Miltie, do us all a favor, and only pull out enough to win!”
And this is why you lost. This attitude of teasing and secrecy, this oh-we-have-so-much-data-we-aren’t-showing-yet act, as deadline after deadline slipped past. If a stolen Presidential election isn’t enough justification to drop the cloak-and-dagger act and present everything you’ve got, what is?
The massive amounts of data are unprecedented and Patrick is one man trying to make it understandable to a wider audience. Why are you Dems so defensive and worried? Biden is the most popular candidate in history with more votes than Obama! Just cooperate like Trump did with the Russia hoax.
I agree entirely with TRN. I appreciate the work Patrick and others have done, but what did it get the country? So many want to blame Trump when, like TRN says, the full presentation of data and PROOF was withheld from him as well as from all of us. It makes this exercise seem opportunistic at best, part of the damage and destruction on the country at worst.
Thank you!! Appreciate all your work and the information!! You are a true patriot!! God bless!!
“I have read all three of Patricks chapters and the preface and find it utterly fascinating.I consider him to be one of the greatest patriots this nation has ever had.
He will be in my next post however it is being held up for reasons I cannot mention.
In conjunction with the information that Patriick has provided I have begun watching this.. https://www.youtube.com/watch?v=xT3hPuY8w5M
I am now more convinced than ever that Trump is not nearly as smart as many patriots and christians think he is. He is simply an opportunist that God placed in the right place at the right time to give the swamp the opportunity to convict themselves and give God the justification to come forth out of his hiding place and vex the nations. Trump was actually used by God to be a disruptor, but he is not any kind of inspired servant of God beyond that..He certainly is no type and shadow of King Cyrus. His time has probably come and gone.
It appears from Patricks narrative that Trump missed a golden opportunity by not following the advice of Patrick and Flynn and Powell, although, it still would have only resulted in civil war which is what will happen anyway. The global cabal is way deeper than any of these people realize.
Patrick and Flynn and Powell (all great patriots} do not get the spiritual/prophetic component of all of this so they are simply dealing logically and constitutionally to the best of their ability.
God will be the remedy.”
Mr. Byrne,
I am constantly perplexed when Constitutional Conservatives ask, “…what can we do?”
You Patrick, have accepted the responsibility to bring dark into light on a macro geopolitical level. Yet if we cannot accept our responsibilities at the micro level, are we not creating our own victim mentality within a partisan echo chamber? I challenge each and every individual to stand before a mirror and recite the words”…I am being socially and economically threatened because of YOU! YOU are the reason why I am exposed to public ridicule and condemnation for expressing my God Given Rights, so eloquently expressed in our Nation’s Founding Documents! How could YOU be so gullible, so misguided, so trusting of people willing to bastardise our Republic for their own greed, for wealth and influence?”
I confess to you all, my Fellow Patriots, the imperfect man looking back at me in that looking glass, wielding accusations of irresponsible “lapses in judgment”…
IS ME!!!
I AM GUILTY AS CHARGED!!!!
When did I last express my opinions to my elected officials at the local, county and state levels? Why did I accept my state “SUPREME(?) COURT” ruling, finding VOTER ID UNCONSTITUTIONAL! This despite being voted on in state balloting! How did my public schools and universities become breeding grounds for Democratic Mob Rule, underpinned by Maoist tactics? How have I found myself employed by a retailer that is clearly a part of an established oligarchy that can determine my ability to make a living, threatening termination for expressing my opinions outside my professional venue?
It is my duty to act, within the law, to make my voice heard…NOW…OR SUBMIT TO TYRANNY.
Thank you, Patrick. I appreciate the time and effort you spend on writing out and publishing your information.
As for all the commenters here and elsewhere, I am done trying to make rhyme or reason out of uninformed, armchair quarterbacks who have absolutely zero first-hand connection or evidence. You all can have your opinions, and they all stink. 😉
Let’s not forget Mr. Jovan Pulitzer’s demonstration!
Spot on, Patrick Byrne.
Now, how do we resolve this corruption in the American Voter’s rightful favor?
Patrick, your information on foreign interference comes from The American Report. Why no attribution?
Proof Positive: Coordinated Cyberwarfare Attack Against US By China, Russia, Iran, Iraq, Pakistan To Steal Election From Trump
https://theamericanreport.org/2021/01/03/proof-positive-coordinated-cyberwarfare-attack-against-us-by-china-russia-iran-iraq-pakistan-to-steal-election-from-trump/
Fascinating read Patrick. It’s difficult for those of us who lack the technical knowledge to follow the voting machines and foreign interference side of it. But wouldn’t be at all surprised. But the “irregularities” were so blatant, so overt, that it’s hard to understand why it was so difficult to make the case. And why didn’t DJT or his designees simply demand audit/investigation/recount etc right away? Inspecting (all of) the paper ballots, or images of originals, seems the only trustworthy approach (J Pulitzer). Along with forensic examinations of machines AND investigative interviews with election officials and staff. Granted, I don’t understand the legal issues involved, but it seems outrageous to me that this much time has passed, and NONE of these things have been done. Is that because DOJ failed to get involved? If so, what recourse is there, on what authority can the necessary investigation be undertaken?
The affidavit comes from Russell James Ramsland Jr., a cybersecurity analyst and former Republican congressional candidate. Ramsland is the one who mistook voting jurisdictions in Minnesota for Michigan towns in a separate flawed analysis of voter turnout. His latest analysis correctly names Michigan voting jurisdictions, but similarly arrives at inaccurate voter turnout rates.
For instance, Ramsland claims that Detroit saw a turnout of 139.29%. The city’s official results show that turnout in the city was actually 50.88% of registered voters.
In a second affidavit Ramsland filed in the same lawsuit Dec. 3, he said that the information source for his first affidavit was data from the state’s open data portal and Secretary of State’s election results page “that no longer exists.”
The Secretary of State’s office never shared township, city or precinct turnout data on its results page, according to Tracy Wimmer, a spokesperson for the office.
It is difficult to imagine that a turnout rate above 100% — let alone 782% in the City of North Muskegon or 461% In Zeeland Charter Township — would have escaped election officials compiling the statement of votes cast. But beyond the implausible turnout rates Ramsland alleges, there are other glaring problems with the list. Shelby Township is named twice. So is Zeeland Charter Township, with two vastly different turnout rates: 90.59% and 460.51%. Ramsland lists “Fenton” without specifying Fenton City or Fenton Township. But the turnout Ramsland lists for Fenton does not match the turnout in either jurisdiction.
The actual turnout statistics reveal the inaccuracy of Ramsland’s numbers. His figure for North Muskegon is off by a factor of 10: The actual number is 78.11%, not 781.91%. For Zeeland Charter Township, he inflated the turnout nearly sixfold. For Grout Township and the City of Muskegon, his number is more than triple the correct number.
Please.
The problem seems to be the public officials are corrupt and involved, too, just like the courts, so not a straightforward proposition. Plus hundreds of thousands of ballots have been destroyed according to witnesses and even a few of the fools who posted videos of themselves destroying them!
Thank you Patrick for the incredible job you have done. You are truly a warrior. Please stay safe. Do you have any thoughts on Steve Bannon -Miles G? Let us know – next steps to take- what we can do with all this information moving forward. Look forward to reading more & taking action to support our USA moving forward. I am hopeful- even though we have take a hard hit. God Bless!
The “dolphin-speakers” term is pretty insulting
I thought it was clever and funny myself.
Almost unbelievable. Gob-smacked at how the keys to the kingdom could so easily be handed over while the people remain blissfully ignorant. Quite probably the greatest heist in human history. I hope this is not the last word on the matter. Keep up the great work Patrick!
Patrick,
Brilliant!
I especially appreciated “No One Said It Would Be Easy”.
To my fellow Americans and Patriots, please try to be patient in the Big Tech world of instant gratification that we live in. Also, read, read, read! Read and listen to everything and anything you can get you hands on and use your critical thinking skills. The answers are out there. Most importantly, they’re within you.
Fascinating read Patrick. It’s difficult for those of us who lack the technical knowledge to follow the voting machines and foreign interference side of it. But wouldn’t be at all surprised. But the “irregularities” were so blatant, so overt, that it’s hard to understand why it was so difficult to make the case. And why didn’t DJT or his designees simply demand audit/investigation/recount etc right away? Inspecting (all of) the paper ballots, or images of originals, seems the only trustworthy approach (J Pulitzer). Along with forensic examinations of machines AND investigative interviews with election officials and staff. Granted, I don’t understand the legal issues involved, but it seems outrageous to me that this much time has passed, and NONE of these things have been done. Is that because DOJ failed to get involved? If so, what recourse is there, on what authority can the necessary investigation be undertaken?
Patrick,
You are one of four people I trust when it comes to the truth and facts about this election fraud to the American people. I am saddened to hear about Mayor Giuliani. I pray for his recovery. I pray for your safety and the safety of our President Donald J. Trump.
Dumbledore to Harry in “Harry Potter and the Half Blood Prince”: “Don’t you see, Voldemort himself created his worst enemy, just as tyrants everywhere do. Have you any idea how much tyrants fear the people they oppress? All of them realize that one day among their many victims there is sure to be one who rises against them and strikes back!”
The Left and the DS fear us more than we fear them. Donald J. Trump rose up against them. This is not over.
I knew it but it is uplifting to see it in black and white! Thanks.
For the “woe is me” crowd, take inspiration from Nigel Farage on the first anniversary of Brexit. Listen to what he went through for twenty-seven years with everyone against him except a small group of supporters. They were vilified by the presstitutes and every political party in the UK and EU. He didn’t demand instant gratification like a toddler. He gives credit to the British people for their perseverance and patriotism.
https://www.youtube.com/watch?v=q2acSQs6zMA
Does anyone here do any due diligence and independent thinking? I suggest you do, Many of the people central here are clowns. From The-Kraken-Sidney, to Rudolph, to Jovan Hutton Pulitzer, to Russell James Ramsland Jr. and even Qnon following General Flynn.I would never cast myself in with these characters.
As to J. Jovan Philyaw, a former infomercial producer.
Philyaw—excuse us—J. Hutton Pulitzer, as he’s now calling himself, says this about himself
“Having personally authored more than 100 ground-breaking patents and known for thrusting forward the momentum and adoption of the Internet, J. Hutton is a leading visionary in the world of marketing, product development, and entrepreneurship.”
“A further testament to Jovan’s genetic instinct to survive, four generations of grandfathers on opposing sides in four major wars created 50-50 odds on both sides against the world ever seeing Jovan’s creative work.”
‘Due diligence and independent thinking’, critical thought, irrefutable evidence, grasp on reality, (basic education) … ? Tom, you’re on the wrong site.
All a side show Tommy to the real event. Disinformation, distractions, etc. I was not surprised at all at the way Rudy G. was running his “operation”. He was a distraction and a “look over here” disinformation op. Trump knew the courts weren’t going to hear any fraud cases. He was looking for another solution, another route all along, and General Flynn knows. He may even be playing Patrick. Or Patrick may even know what is really going on and contributing to the distraction. This is all a game until Trump reveals the end of the movie. You all do know that Mnuchin is a Hollywood producer, right. Sit back, relax, chill out and enjoy the show.
I hope every one is following what is going on in AZ and their audit very closely. Every one should call and give the State Senate president our support. They are fighting hard to forensic audit the paper ballots and the Republican election board is fighting them still. Even after they admitted in court that the legislature has full power over all election matters.
If we can get the original ballots and let Jovan scan them, then we can catch them red handed. Or prove that we were all wrong. Then the other states will have to let it happen. If they haven’t spent the last 60 day in a boiler room hand marking up a few hundred thousand new ballots.
I seem to recall some controversy over who is auditing the ballots. The two companies selected, if they are still in the running, were connected to Dominion which makes it an exercise in futility.
Bottom Line – it doesn’t matter how it was rigged/stolen. Nothing was done about it except that thousands were called to DC on Jan 6 for some “new revelation” that never materialized from Trump.
Hundreds were caught up – most innocently – with bad actors. And thousands more are now deemed Domestic Terrorists who will be cancelled in life, put on the No Fly List, hunted down and lives destroyed and/or put in prison.
And for what?? Trump walked away never using the power he was given. Sending our Nation into the Communist/Oligarchs control for the Great Reset. Either due to a lack of courage or ineptness I do not know.
For that I will never forgive him or the Nation of criminals running the Cabal.
But I will no longer abide by anything nor will I ever vote in this corrupted system again.
Try to understand who or why created the Capitol riot? Trump had the plan to reveal the fraud during electors vote disputes on Dec 6th. The Deep State had to stop by any means possible. They being the evil they are had this plan to create this false flag operation ‘riot’ to stop the revelation that was coming. Trump fell into their trap is my opinion. The Democrats and the Deep State were ready to do anything to stop Trump, all for hiding their own crimes.
The military is in control right now. Can’t you all see this? The fencing and troops in DC. The White House is dark. Kamala has not even moved into the VP residence. No temporary flight restrictions (TFR) in Mar-a-lago….the list goes on! Too many weird things happening. Trump flew out on AF1, Biden takes a civilian plane to DC for his “inauguration”…. Trump did NOT walk away and abandon us! Stop! Just stop it.
The packet captures are very compelling however it only shows apparent connection attempts. Packet captures can show much more than that, i.e. actual authentication and connection and the actual data being transmitted. Do they have that information? Maybe I missed it but if that information is available, it’s irrefutable – game over.
From a patriot:
During the last four years, did patriots in the military release information about corruption to wake up the citizenry?
Did the military hope that citizens would use elections to remove corrupt people from power?
How did the DC swamp overcome the record turnout of Trump’s base in November?
Rig the vote for Biden?
In a delicate procedure where the risk of harm is significant, are the least invasive methods tried first?
If the first attempt is unsuccessful, are more invasive methods considered?
Did the military try the least invasive method of removing corruption?
Did the first attempt fail?
Why?
Corrupt politicians still control elections?
Does the military have other (more invasive) methods at their disposal?
Did President Trump do everything humanly possible to expose corruption?
“I left it all on the field.”
What was the response of the DOJ, governors, mayors, state legislators, Congress, and the courts to evidence of corruption?
Turn a blind eye?
Having given them the opportunity to address corruption, can the military step in?
When non-military institutions and agencies refuse to deal with corruption, who enforces the rule of law?
What is the last line of defense against anarchy and tyranny?
Military?
Was President Trump’s term in office good for the military?
Rules of engagement changed?
Troops home from foreign wars?
No new wars?
Military pay raise?
Improved VA healthcare?
Was Trump’s term in office good for the world?
Peace with North Korea?
Peace in the Middle East?
Would the military trust Trump with the fate of the nation?
Why?
Proven track record?
Did Trump hint that he would be back in office?
Why?
If the military planned to intervene in the Biden administration, would Trump know?
Were there protests in Washington D.C. during Biden’s inauguration?
No?
Why did the military build a fenced and guarded perimeter around the Capitol?
Does the military plan to keep 7,000 National Guardsmen in DC through mid-March?
Why?
The military is the only way.
Yes.
No. None of these things happened because the election was free and fair. You just cannot bear to accept it.
Trump actually did accept it, as information from people there during his unraveling shows. “Can you believe I lost to that guy? That corpse?” He saud it, he knew it…he tried, totally undemocratically, to overturn it.
Then this nutcase Byrne and crew showed up. Trump mocked them, putting Powell on speakerphone, encouraging her, then mute button to mock her.
Then they got inside his never strong head abd he began to think it was worth a try.
Just think about that. The biggest democracy in the world. Your nation goes about, murdering helpless people worldwide, all in the name of democracy… and your own president wouldn’t accept defeat.
By the way.
You are not the envy of the world . Europe, Britain, Hong Kong, we despise you. You can’t even give yourselves healthcare. We live free from fear of sickness. You are slaves to insurance companies ….you don’t even have the common sense to vote for the person that would give you what all Europe enjoys.
No, you are so backward you call it freedom to have your money taken off you… you have to beg insurance companies to take it.
We pay National Insurance. And get top care. You believe lies about our systems.
In my whole life, I have never heard anyone say a good word about America. Always total disgust. Your fat, your greed, your stupidity, and now this. God, you are detestable.
I read the important pieces of what you had to express and I’m a military veteran of 2 branches of the military and I’m highly decorated with a letter of recommendation from the commander of the joint chiefs of staff. I was fortunately able to squeeze in an MBA from Wharton and was a professor in Taiwan for some years. After years of hard work and sacrifice I’ve reached a respectable level in life. We are contemporaries in the sense we are the same age. I’ve never been married and that’s the only thing I haven’t accomplished heretofore. I have hung on your every word since the election hoping and praying for the best and your words here confirmed my worst nightmare. I’m heart broken that a country I fought for and my friends (Pat Tillman) gave their life for seems lost in the abyss. Thanks for your attempts to rectify a bad situation. God bless you!
I just wish we could live in a world where we could trust things. It’s exhausting lately. I just want a world where we can see the truth.
Can we vote our way out of this system?
The November election proved that we can’t.
You know you are hitting it when the bots, trolls come out.
Lawsuits are expensive.
Complex ones are even more expensive.
Complex lawsuits with hundreds of witnesses in multiple states/counties to be interviewed,
affidavits/declarations taken are even more expensive.
Multiple complex lawsuits in multiple jurisdictions (counties, states, appellate, SCOTUS) are prohibitively expensive.
Fees and costs (hotel, court costs, filing fees, staffing, access to cases/legal precedent, meals, travel, (many involved in multiple states), hundreds of hours times (x) many, many from staff to legal consultants/experts/expert prep/etc; legal writings/briefs; hearings (prep and attendance); team/staff meetings, and much, much, much more).
Easily millions and millions of dollars spent (even if some participants waived some or all fees, although most were probably reimbursed for expenses at the very least).
Innocent question: Which foreign elections has the United States not had its sticky little fingers in? I’m not just talking vote manipulation but also instigation of coups d’etat and political assassinations? Certainly not convinced there was foreign interference here, although I remain open minded.
Just saying, if you lot are gonna dish it out, you gotta learn to take it.
PLEASE do NOT confuse the Cabal with either the United States or the American people. Thanks.
Fair question, fair’s fair. Deep state ran its military operations through the US. The mission to end the deep state is designed to fix that problem as well
Fair question, Fair’s fair. Cabal has historically used the US for its world dominance. The removal of the cabal fixes that problem as well.
This isn’t chapter 2. Chapter 2 would be one in which you pick up where you left off ending Chapter 1.
No wonder Steve Bannon said they’re working on stopping the steal but “none of this crazy Italy and connected to satellite stuff”. Looks like Bannon and Byrne aren’t friends. Now I’m confused.
You realize you actually don’t say why how it was lost from Donald Trump ….this is a big nothing burger as usual…… Yes there was election fraud we all know that but how was it now shown to all parties that could have done something ? you left off chapter 1 you by hook or by crook were going to a meeting with Donald Trump then in chapter 2 all you say is the same hashed out stuff we already know… is there a chapter 3? Or ?
Item 16 is misleading. The document referenced in Item 16 is not an assignment of patents. It is a security interest recorded in case the bank was not repaid on its loan.
While all are you are wondering “what do we do now?” the kids with their $600 stim checks and phone apps are taking back our money from the hedge funds, exposing the corruptions between big tech, wall street and the banks, and UNITING the right, left and center.
This is much more than an epic wall street battle, this is the working class saying fk politics and fk ideology we want our money back and fair access.
The British Crown on orders of the Queen stole the US election using the Canadian CROWN Company Dominion Voting.
For those wishing to see actual vote switching, here is a spreadsheet I compiled showing the switches that occurred in Pennsylvania after 76 pct. The algorithm change is apparent here because it’s the first instance in a systematic series in which votes are subtracted from Trump’s total and moved to Biden — or are moved to Leftover votes (Other). The Leftover votes are transferred to Biden a few transactions later. This is a consolidated list of transactions because there are approximately 400 transactions from 11-4-2020, 19:45Z to 11-11-2020, 23:45Z.
https://revealthesteal.blogspot.com/2021/01/pennsylvania-vote-switches-after-76.html
Prior to the algorithm change, votes were being shifted to and from the Leftover votes — with the exception of a single shift of approximately 17,800 votes from Trump to Biden.
https://revealthesteal.blogspot.com/2020/11/pa-algorithm-needed-tweaking-to-give.html
You seem to have used the Edison data source. As I pointed out, this data is useless, since it does not represent accurately the state of tabulation. Also, you are inferring Trump and Biden vote totals from a vote-share percentage with 2-3 decimal places, which leads to a huge rounding error.
There are no vote reductions in the actual tabulation data. The vote reductions in the Edison source result from manual data entries & rounding errors. In the coming days, I make some Scytl data available to compare to the shitty Edison source.
Nice try, but you’re incorrect. The reductions are not from manual entries and rounding errors because 1) the manual entries stand out like a sore thumb and I did not include them in the vote manipulation and 2) a rounding error does NOT subtract votes — as in NEVER.
In fact, the Edison Results almost match Pennsylvania’s certified results perfectly — with the exception that Pennsylvania has decided to not report any write-in votes — but Edison does.
TOTAL Biden (D) Trump ( R ) Jorg (L) WriteIn
NYT/Edison 12.12.2020 6,925,237 3,459,923 3,378,263 79,379 7,672
Certified Pennsylvania Result 6,915,283 3,458,229 3,377,674 79,380 0
Differences 9,954 1,694 589 -1 7,672
The key to the fraud was in the switching of write-in votes. Pennsylvania’s official results show no write-in votes — and that’s impossible because the Green Party presidential candidate was not on the ballot and had to be written in. Green Party statewide candidates received between 31-38K thousand votes — and Pennsylvania wants people to believe that NONE of those 31-38K votes wrote in their candidate for President.
FRAUD!
BTW, Scytl data is Edison Data. I’ve already looked at both.
Biden Votes Trump Votes Other
NYT/Edison 2,474,290 2,464,293 59,983
GA Sec of State 2,474,507 2,461,837 62,138
Difference 217 -2,456 2,155
Very similar totals.
https://results.enr.clarityelections.com/GA/105369/web.264614/#/summary
From Edison Research (my EMPHASIS added):
Vote Count
The NEP provides media organizations with REAL TIME VOTE RESULTS in all 50 states for statewide races, ballot initiatives and House races. The NEP VOTE COUNT from Edison Research is the only service continuously updated after Election Day. We TRACK EVERY VOTE until results are certified by all states. Vote count data is available for statewide results, vote by Congressional District, county vote data breakouts for statewide races, and all U.S. House races.
https://www.edisonresearch.com/election-polling/
Well, isn’t the call was pretty clear? – the DNI report assessment has already made it. John Radcliffe has stated it’s foreign interference on Fox interview with Maria even before the report was out. Despite the report and his assessment got delayed and didn’t came out until Jan 7, but it pretty clear – there is a foreign interference.
Steve Bannon had he retired 3 star Air Force Gen McInerney warmed us about the hammer and score cards that “They Will Steal this Election” back in Oct, don’t you think Trump had already known and got this before we learned everything, or he was just genuinely stupid to be the last person to know things? I am still wondering why Trump still put Christ Miller as Act Sec of Defense after he had lost the election? Why Christ Miller installed Michael Ellis a Trump loyalist as the top lawyer at NSA? Why did Sec Pompeo twitted every 1 hour, 30 mins, 15 mins just like those rumors said, and with the pictures of “We the People”, “1776” and “George Washington crossing Delaware River” on this last day…just so many puzzles. I don’t know what’s going on, but in my gut I feel Trump knew this is not just about the election anymore, the scale of the involvement is way far beyond that, considering many countries and our internal enemies got involved. He wanted to be unpredictable . If we knew Trump’s plan, so does his enemies.
About Miles Guo. He had been actively using his Whistleblower movement as a platform to support Trump and claimed Trump a guaranteed 1000% win for re-election. But on the 20th of Jan when Biden inaugurated, he and Lu De from the Whistleblower movement immediately changed their tone and swiftly urged to support Biden Kamala admin, denied their support for Trump. Before the election, when Hunter Biden’s photos were exposed to the public in his network G-TV, he claimed he got the hard drive of Hunter Biden’s laptop from his connection from Jiang Zemin, Zengqinghong and Meng Jianzhu, Xi’s opposition in the CPP in China. But we knew the laptop from hell is from the owner of the computer repair shop in Delaware. He has been using this platform to promote to sell his G series (G-Club, G-Coin, G-Fashion) to his followers. Do you really trust a guy like him telling you who is a traitor? so who do you believe? You Make the Call..
i really want to believe you and i really want all that to be true man but at a face value you can see where the hope gets distorted or lost.. but i do agree with what you said BUT i also want you to think about someone telling you if you continue to pursue this we will make you the next JFK… every one is tough as nails until their life being taken becomes a actual threat
https://newsla.localad.com/2021/01/31/note-to-arizona-senate-from-a-former-international-audit-executive-if-audit-resources-are-limited-focus-on-the-ballots/
A month ago the Arizona Senate voted to have the audit performed and the MCBOS sued them to stop the audit. Then once the inauguration occurred the MCBOS agreed to have their results audited but they would select the auditors. This was so the MCBOS could choose an auditor who would rubber stamp their results. The MCBOS even stated they would only use EAC certified auditors which limited the population of auditors to the two firms of their liking but then we pointed out that these firms weren’t currently certified.
WE CAUGHT THEM: Arizona’s Maricopa County Board of Supervisors Lied – EAC Updated Website after Gateway Pundit Report Discovered Their Auditors Were Uncertified
So yesterday the Arizona Senate decided to stop playing games and they decided they would choose the auditor to dig into Maricopa County results themselves.
HUGE NEWS! Arizona State Senate Hires Its Own Independent, Qualified, Forensic, Auditing Firm to Analyze 2020 Results
The Senate is doing the right thing. We knew the results of the 2020 election were fraudulent early on. We studied the results and performed our own analytics, and even at a high level we were able to prove the election was stolen by Joe Biden:
Keep an eye to AZ and support their State Senators, this might be our last hope to get to the bottom of all this.
Not ALL is as it seems……
Im trusting this information is being used effectively. When States fail, Courts fail, Congress fails – the legal path outlined by the US Constitution is the US Military. We need the light of day. Its transparency not censorship, not banning, not deletion, not demonetizing your political opponents. Its about Ideas Policies and Results. Apparently they cannot play on a level playing field. Truth Justice and God Speed
What a complete loser of a country; can’t even run an election (apparently). Maybe you should call in the United Nations to supervise next time. Oh no, I forgot, the UN is full of communist operatives. Then how about a neutral country like Finland. A bit embarrassing but at least it would be clean. Or maybe it was clean. Afterall, it was the Republicans who were in charge, right. Just because you lost doesn’t mean you won!
4. Dominion Voting Systems is owned and controlled by foreign entities. We lose control of the data when it goes to a foreign country.
And there goes this one’s credibility down the drain.
The fact that the company that makes the voting machine is owned by a foreign entity doesn’t mean the data goes to a foreign country on election day. Anyone who actually DOES know the technical aspects of the internet knows that.
But since your audience is the vast majority who don’t know technical aspects of the internet, it doesn’t matter, does it?
I humbly implore each of you who wants to LEARN about the voting system in the US to begin exploring the EAC website, where all the systems and their testing are explained and documented.
Who among us really knows how a “Dominion voting system” actually operates? The answers are on that website.
Find out what’s used in your state, and learn all about it.
Understand where the weak points are – they always involve PEOPLE, not machines.
Think about how the results could be audited thoroughly. It starts with voter registration, then goes to who is voting, ballot completion, ballot scanning, storage of results, transmission of results, counting of results.
9. Dominion Voting Systems is based in Toronto, Canada, and assigns its intellectual property including patents on its firmware and software and trademarks to Hong Kong and Shanghai Bank Corporation (HSBC),
Hmmm, guess they missed patent no. 8913787, with applicant “Dominion Voting Systems, Inc.” and assignee “Dominion Voting Systems, Inc.”. Not “HSBC”.
cve.mitre.org? Isn’t MITRE some kind of CIA outfit? Didn’t Heidi Avery work for Mitre back in the early 2000’s? Wasn’t she JB’s right-hand man at the NSC/CIA?
i love you pat ty for these stories they are greatly appreciated
Regarding the excel file:
Mac addresses and IP numbers are spoofed easily. Has that been taken into account?
I looked at some of the listed “owners” randomly, and found some that surely were no perpetrators. (Why would a small privately owned European manufacturer of bathroom fittings with no Chinese staff run such an attack, during their working hours no less?).
So either their IP was used, or their IT systems hijacked.
Can we get a bit more info on this please? Thank you.
Byrne is a Billionaire with no incentive to place himself in harms way, so any idea that he is fabricating anything is ridiculous. All you gas lighters out there can continue to pretend like the election was pristine, but you will NEVER change the facts. It was stolen, plain and simple, and the current administration is illegitimate along with everything they do from 20 Jan onward. We are in Presidential purgatory, and all will not be well until all of the truth gets into the courts for real; which it will. Oddly enough, the idiot Dominion company suing people will begin the discovery phase in earnest, and the fraud is too big fir them to hide or clean everything. No doubt they have been trying, but server logs are everywhere, and they will tell the quiet story of a million fingers tickling keyboards to make Biden the winner.
So with all this information available why did President Trump not take at least the minimal approach to federal intervention in the 6 counties with federal marshals and US Army support to get those key epicenters of fraud audited and corrected and new results sent to the electoral college from the State’s legislatures. Governors and Secretaries of States jailed and incarcerated who refused to convene their state legislatures into session to correct the fraud?
Patrick, Amazing work.
I watched Mike Lindell’s video, and he had Mary Fanning on at the end.
She showed a fraudulent version of this spreadsheet, where it was amplified into MILLIONS of votes.
I didn’t realize it at the time, but she appears to be a grifter and a fraud.
Mike Lindell is a good man, but he appears to have been deceived. If you agree, then please call Mike out on this.
What a pack of lies. I hope Dominion and Smartmatic go after Byrnes fortune. How do you attack machines that are not connected to the internet ?
Bear in mind Byrne says it was done through”smart thermostats, remotely breached”.
Some people watch too many movies .
And those movies, like the Avengers, are now too realistic. Minds softened by soft life, too much food, greed, minds distracted by the breakdown in norms, standards, etiquette, minds tha aren’t free…American people are the least free in the Western world, yet believe they are the most free… these minds can’t be expected to make serious judgements.
Stop reading the bullet points of the internet. Try reading a long serious classic, and see if you can concentrate.
If you can’t, then you are the kind of person who would believe this shit.
Couldn’t have said it better myself, Fiona. No wonder the United States is going down the drain with such feeble minded idiots in its populous. The whole country needs to revert to factory setting and start again.
Couldn’t have said it better myself, Fiona. No wonder the United States is going down the drain with such feeble minded idiots in its populous. The whole country needs to revert to factory setting and start again.
the visual graphic shows a target in Austin Texas and Oklahoma city but Texas and Oklahoma are not on the spread sheet?
Patrick,
According to your excel spreadsheet, the stolen votes flipped AZ, GA and PA.
MI, NV fell short of flipping election.
WI not referenced.
(I’m looking at the PT sheet that summarizes by state and foreign countries)
But your narrative indicates all states flipped.
So, which is it?
Patrick,
The spreadsheet was apparently compiled by your cyber experts.
But where was the source/raw data from?
Packets?
Lindell’s Absolute Proof appears to reference the same data.
And Mary Fanning mentions that voting machine vulnerability was
brought to the attention of Comey (FBI) in 2015.
Was a surveillance system put in place then?
Do/did your cyber experts have access to it?
“James Comeys appointment will be for an initial three-year term which, subject to re-election by shareholders, will expire at the conclusion of the 2016 Annual General Meeting.” -HSBC Bank… Wasn’t Comey investigating In 2015? Dominion Voting Systems based in Toronto entered into a Security Agreement with HSBC Bank
https://www.theguardian.com/us-news/2015/feb/10/hillary-clinton-foundation-donors-hsbc-swiss-bank
There’s a lot of information here, but something very important that is missing is an actual identification of a vulnerability. There is no mention of a specific vulnerability identified or reported. If you want to see what these look like, there are tens of thousands here: https://nvd.nist.gov/. So, there’s a lot of smoke, but no smoking gun and no fire. Keep looking, and if you find an *actual* vulnerability, then report it. Otherwise, all you have is a lot of speculation.
Make $6,000-$8,000 A Month Online With No Prior Experience Or Skills Required. Be Your Own Boss And for more info visit any tab this site Thanks a lot just
open this link…………………….. Www.Wpays99.Com